Context-based data classification
Avoid false positives with a context-based DLP
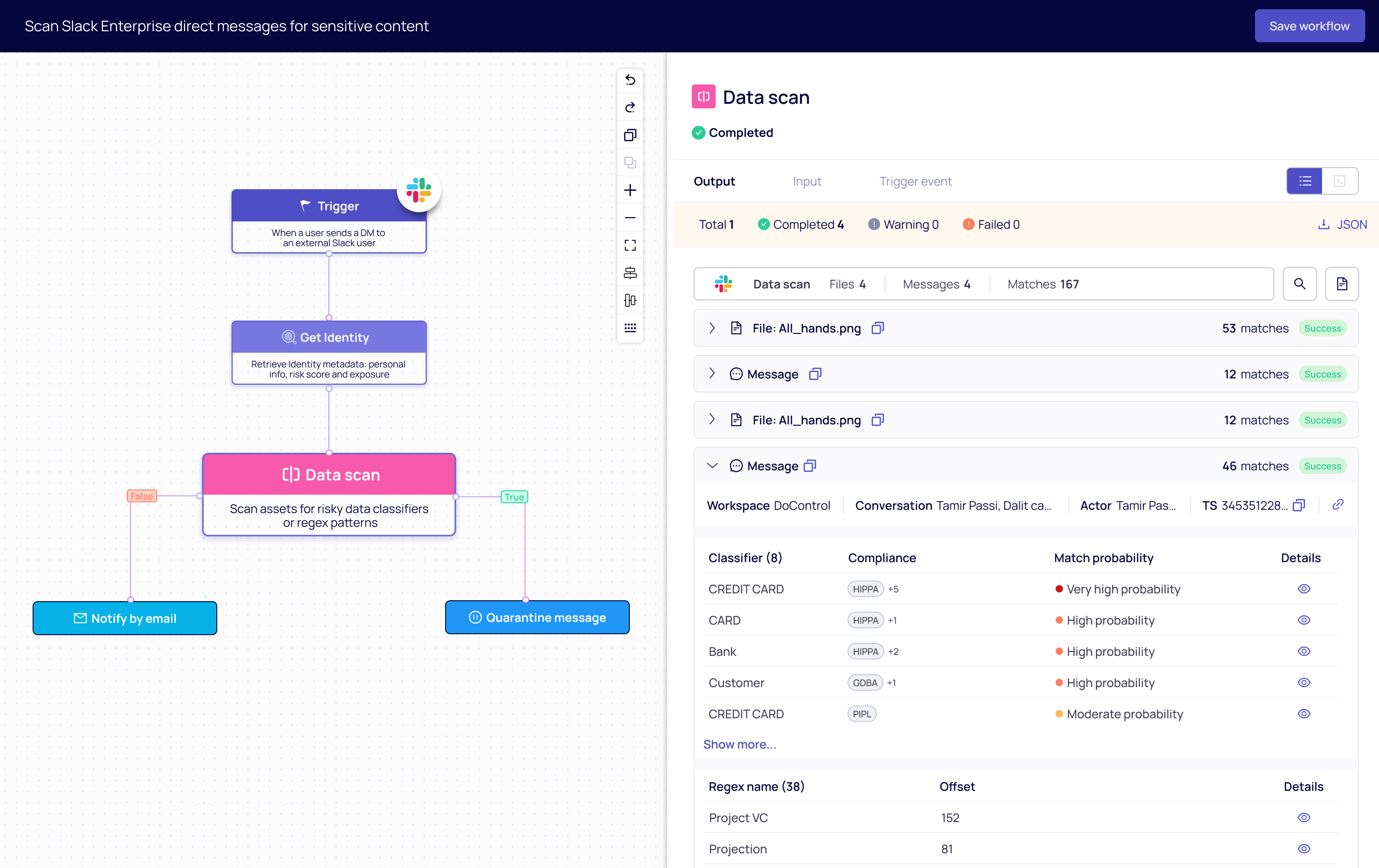
DoControl’s DLP solution utilizes a combination of custom keywords, RegEx, and business context from IdP, EDR, and HRIS to distinguish between normal business activity and actual data loss, ensuring a more intelligent and accurate DLP strategy.
This approach enhances SaaS security, ensuring that sensitive information is protected while allowing secure access to authorized users. With advanced monitoring capabilities, organizations can effectively mitigate security risks and maintain compliance across SaaS applications.