
Twenty years ago, business was anchored on-prem. Today, it is built on SaaS, and identity is the new perimeter. This transition has fueled global collaboration and speed, but it has also opened the door to a new category of security risk: threats from within.
Unlike traditional external attacks, insider threats originate from trusted identities: employees, contractors, third parties, or even non-human identities operating within the environment.
While these threats don’t always come from malicious intent (although, many times, they do…), data exposure happens because of:
- Accidental oversharing or misconfigured permissions
- Employees accessing or downloading data they shouldn’t
- Departing employees taking sensitive information with them
- Third-party collaborators retaining access longer than necessary
- AI agents or automation interacting with sensitive data without proper controls
At the same time, SaaS platforms make it incredibly easy to move data. A single action - downloading a file, sharing a link, or exporting a dataset - can expose critical business information in seconds.
This creates a fundamental challenge:
How do you trust users & enable the business while still protecting your data?
This is where insider risk management becomes essential.
At a high level, effective insider risk management enables organizations to:
- Monitor how trusted identities interact with sensitive data
- Detect risky or anomalous behavior in real time
- Understand the context behind user actions
- Prevent data exfiltration before it happens
- Protect sensitive data without disrupting day-to-day work
- Remediate data exposure in real time once insider risk is detected
But traditional approaches fall short.
Legacy solutions often focus on alerts after the fact, lack visibility into SaaS environments, and fail to account for identity context or behavioral signals.
Modern organizations need a new approach - one that is identity-driven, context-aware, and built for SaaS.
What Is Insider Risk Management?
At its core, insider risk management is the ability to identify, understand, and reduce risks associated with how trusted identities interact with data within an organization.
It answers a critical question:
Is a trusted user - or identity - interacting with data in a way that could introduce risk to the organization?
In SaaS environments, insider risk management goes beyond simply monitoring employees or stopping isolated incidents. It focuses on understanding behavior, context, and intent across all identities with access to data, including:
- Human users (employees, contractors, vendors)
- Non-human identities (AI agents, OAuth apps, service accounts)
- Third-party collaborators with access to internal data
A modern insider risk management strategy provides visibility into:
- Who is accessing sensitive data
- What data is being accessed
- How data is being used, shared, or downloaded
- When and where access is occurring
- Whether behavior aligns with normal patterns
But visibility alone is not enough.
To be effective, insider risk management must also enable organizations to take action.
Within SaaS environments, a comprehensive strategy typically includes:
- Behavioral monitoring: Understanding how users interact with data over time and identifying meaningful deviations from normal patterns
- Access and activity analysis: Continuously evaluating who has access to sensitive data and how that access is being used
- Detection of anomalous behavior: Highlighting unusual downloads, sharing activity, or access patterns that may indicate elevated risk
- Context-aware risk evaluation: Incorporating signals such as role changes, employment status, device posture, and behavioral shifts to better understand intent and risk level
- Real-time alerting and guided response: Enabling timely, proportionate actions (such as step-up authentication, user coaching, or access reviews) rather than only reactive blocking
- Automated risk remediation: Reducing exposure through adaptive controls, such as revoking access, prompting justification, or preventing high-risk actions when necessary
In short, effective insider risk management for SaaS ensures that trusted access is continuously evaluated, understood, and guided - so that everyday behavior doesn’t evolve into unmanaged risk.
Emerging Trends Shaping Insider Risk Management
Insider risk management is evolving.
It’s no longer just about monitoring employee behavior - it’s about understanding how identities, automation, and AI systems interact with data, often in ways that are difficult to detect.
Two major shifts are redefining insider risk today: the rise of non-human & AI-driven identities, and the growing importance of context.
Non-Human Identities and AI Acting on Behalf of Users
Not every action in a SaaS environment is performed by a human.
Today, non-human identities (NHIs) - including AI agents, automation tools, OAuth applications, and service accounts - are constantly interacting with sensitive data.
What makes this especially challenging is that these identities often operate on behalf of real users. For example, consider an employee named Jane Smith.
On the surface, everything looks normal:
- Jane is accessing files within Drive
- Data is being shared between Jane and her colleagues
- Jane is downloading documents
All of this activity is tied to Jane Smith’s account.
But in reality, it’s not Jane.
An AI agent or third-party integration has been granted access to her credentials, and is performing these actions programmatically.
In Google Drive, 40% of all events are done by non-human AI identities. In Slack, this number jumps to 53%. And in Sharepoint, the number is 70%.
From a traditional security perspective, this behavior appears legitimate - because it is tied to a trusted identity. But in practice, it introduces significant risk:
- The volume and speed of activity may far exceed normal human behavior
- The data being accessed may fall outside of Jane’s typical responsibilities
- The actions may be happening without her awareness
This creates a dangerous blind spot where non-human activity is indistinguishable from legitimate user behavior.
Why Context Is Now the Defining Factor
In this new reality, identity alone is no longer enough to determine risk, because on the surface, everything appears to be coming from a trusted user. This is where context becomes critical.
Let’s revisit the same scenario.
If Jane Smith typically accesses marketing files from her office in California during business hours, that behavior is expected.
But now, “Jane Smith” (in reality, an AI agent operating on her behalf):
- Begins accessing sensitive product roadmap data
- Downloads large volumes of files outside of her normal working hours
- Initiates activity from London, when she’s based in L.A
- Shares data with external and unapproved email domains
The action itself - accessing or sharing data - is not inherently risky. But the context surrounding the behavior tells a completely different story.
This is what modern insider risk management must solve. Security teams need to understand:
- Who is actually performing the action?
- Is this behavior consistent with the user’s role?
- Does it align with historical patterns?
- Is this being performed by a human - or an automated system?
- Does this activity make sense in the context of the business?
Without context, organizations are left with limited options:
- Trust all activity tied to valid credentials
- Or block behavior that may actually be legitimate
Neither approach works.
The Shift to Context-Driven Insider Risk Management
As non-human identities and AI agents become more embedded in SaaS environments, insider risk management has to change.
It’s no longer about monitoring users - it’s about understanding how identities behave, why they behave that way, and whether that behavior aligns with expected patterns.
This shift toward context-driven security is what allows organizations to:
- Detect insider risk in real time
- Differentiate between normal and anomalous behavior
- Prevent data exfiltration without disrupting productivity
In a world where machines can act as users, context is the only way to separate signal from noise.
How DoControl Solves Insider Risk Management
DoControl was built to solve one of the most complex challenges in modern SaaS environments: detecting and preventing insider risk without disrupting the business.
Most insider risk management tools and solutions rely heavily on alerts and manual investigation. They flag activity - but often lack the context and response capabilities needed to actually stop risky behavior.
DoControl takes a different approach.
We combine user behavior monitoring, business context, identity intelligence, and automated remediation to not only detect insider threats, but prevent them in real time.
Because in today’s SaaS environments, insider risk isn’t just about users: it’s about identities, behavior, and context.
1. User Behavior Monitoring and Real-Time Detection
You can’t stop insider risk if you can’t see how users behave.
DoControl continuously monitors user activity across SaaS applications to detect risky actions as they happen, including:
- Unusual file access or downloads
- Abnormal sharing activity
- Access to data outside of a user’s role
- Sudden spikes in activity
Using AI-powered detection, DoControl identifies potential insider risks in real time, not after the fact.
This allows security teams to move from reactive investigations to proactive risk prevention.
2. Business Context Enrichment
Not every unusual action is a threat, and not every normal-looking action is safe.
This is where DoControl’s context engine becomes critical.
DoControl’s ITDR module enriches every action with business context by integrating with:
- Identity Providers (IdPs)
- HRIS systems
- EDR and security tools
This provides visibility into:
- Employment status (ex: two-week notice, role changes)
- Department and role
- Access privileges
- Organizational relationships
By correlating these signals, DoControl can distinguish between:
- Normal business behavior
- Risky or anomalous insider activity
For example, sharing files to a third-party auditor during tax season may be expected behavior, but downloading sensitive data in bulk after a role change or resignation introduces a completely different level of risk.
3. Identity Threat Detection and Risk Profiling
In SaaS environments, insider risk is fundamentally an identity problem.
DoControl builds a risk profile for every identity - human and non-human - based on:
- Access patterns
- Permissions and privileges
- Behavioral activity
- Contextual signals from HRIS and IdP systems
This allows security teams to:
- Identify high-risk users
- Detect compromised or misused accounts
- Prioritize investigations based on real risk
As we’ve seen, identities can be used by both humans and AI agents - making it critical to understand not just who the user is, but how that identity is behaving, and why.
4. User Behavior Anomaly Detection
DoControl establishes behavioral baselines for users and departments, allowing it to detect deviations that may indicate insider risk.
For example:
- A finance employee suddenly accessing marketing or product data
- A user sharing an unusually high number of files externally
- Activity occurring outside normal working hours or locations
These anomalies are surfaced in real time, giving security teams immediate visibility into potential insider threats. This ensures that risks are identified as they emerge - not after damage is done.
5. Automated Remediation and User-Level Response
Detection without action is not insider risk management. Most solutions can surface anomalies and offer visibility, but they offer no way to actually remediate that risk in real time. Knowing you have a problem doesn’t solve it.
DoControl enables organizations to take immediate action to stop risky behavior through both on-demand and automated remediation.
Security teams can:
- Revoke or modify user permissions
- Remove external collaborators
- Restrict or reverse data sharing
- Suspend or deactivate users
- Cut off access across SaaS applications
DoControl’s automated remediation workflows run 24/7. Once policies are defined, DoControl can automatically respond to insider risk in real time through workflows such as:
- Removing access when a user changes roles or leaves the company
- Blocking or reversing sensitive file sharing
- Revoking access after anomalous behavior is detected
- Triggering alerts or escalation to management
- Time-boxing access to sensitive data
These workflows allow organizations to contain insider threats instantly, rather than relying on manual intervention.
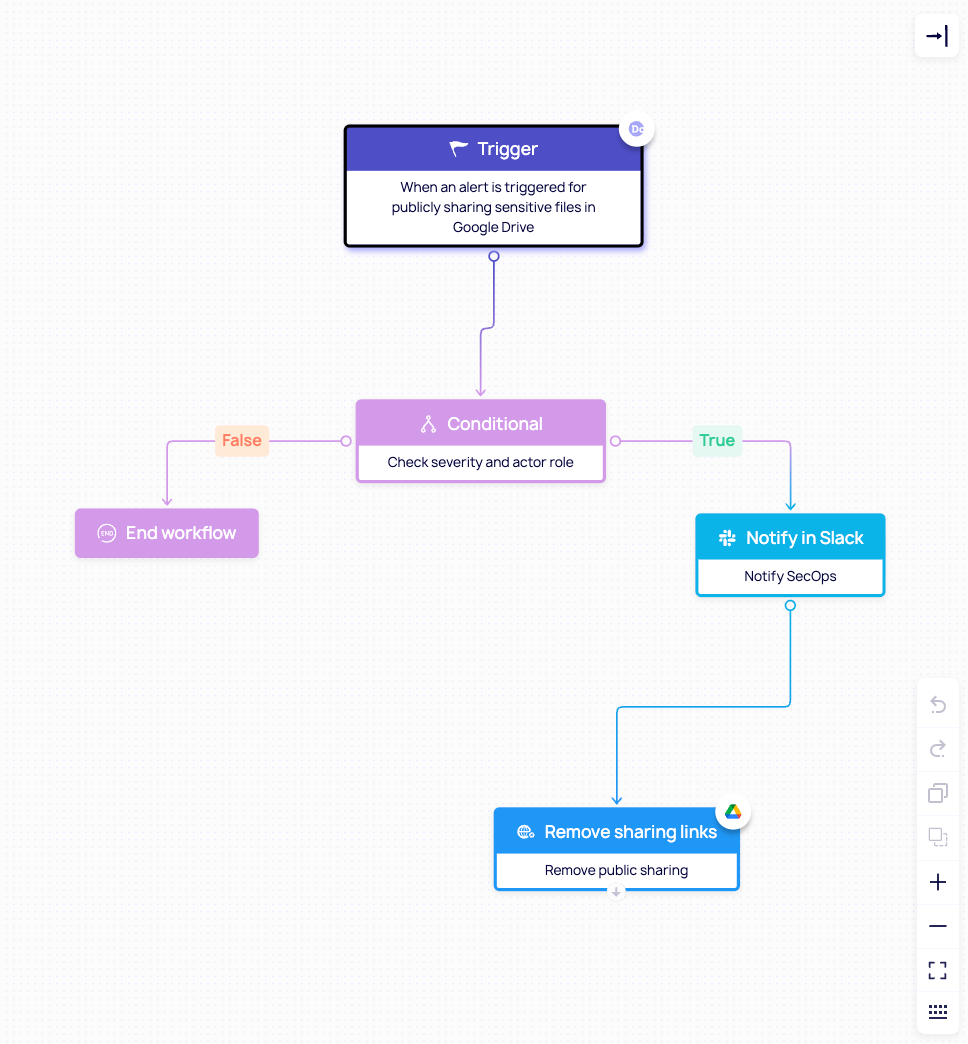
Here’s an example of a workflow that removes the public sharing of sensitive files.
Let’s say an employee shares a confidential document containing PII to someone outside the organization. They might not have meant to share that file publicly; but they did nonetheless. DoControl’s workflow notifies the security team before revoking the share entirely.
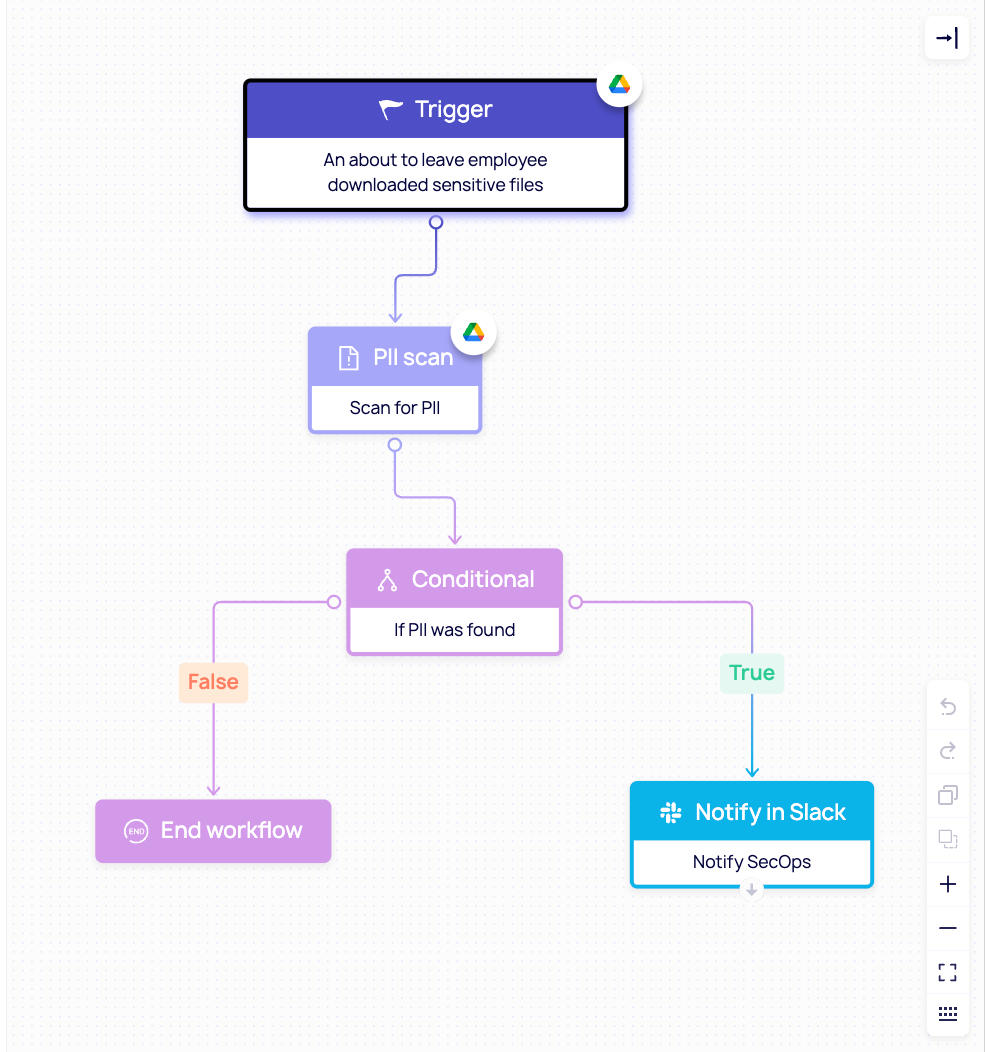
Here's another example of a workflow that prevents insiders from exfiltrating data.
An about to leave employee (this context was gathered from HRIS and IdP systems) downloads sensitive files (probably to take with them to their next firm). The DoControl workflow notifies the security team for their swift intervention.
6. End-User Engagement and Education
Not all insider risk is malicious, many incidents stem from human error. DoControl can address this by engaging users directly at the moment of risk.
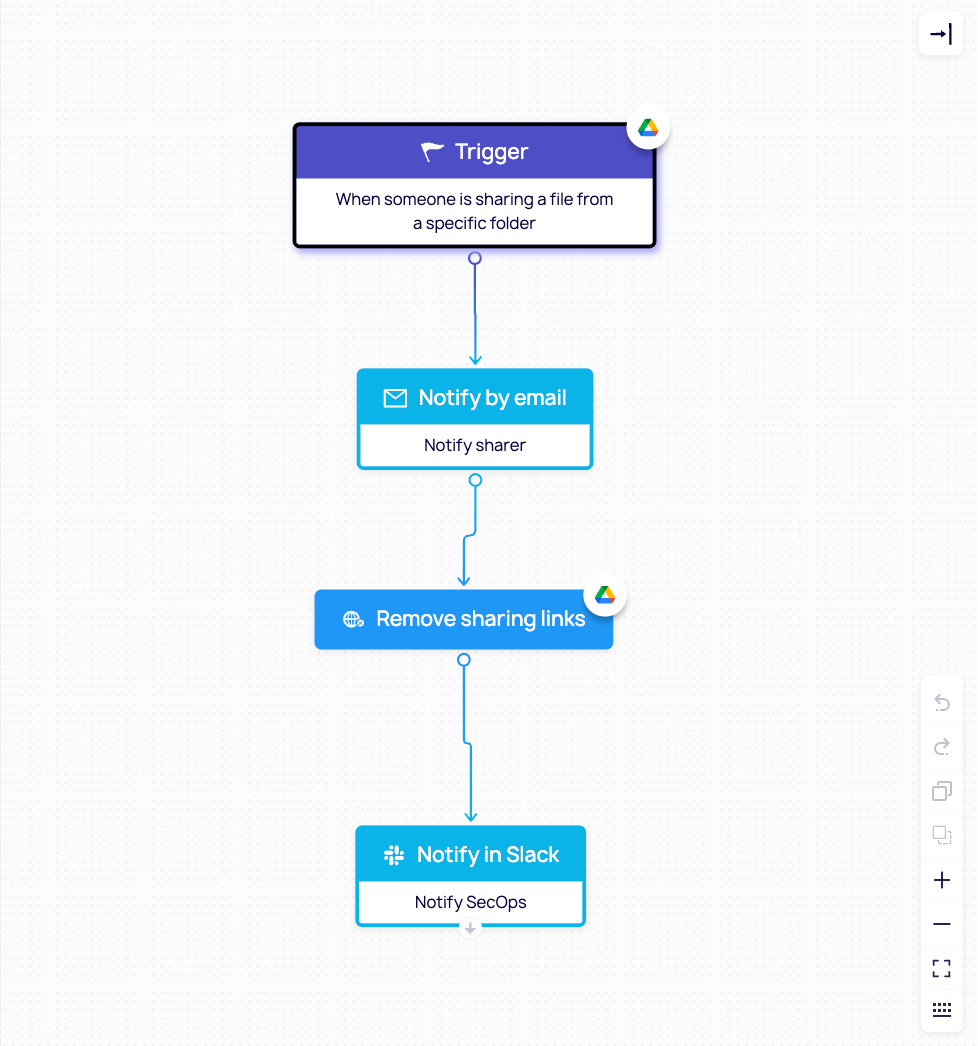
Here’s an example: an employee shared a file from a specific folder that looks like anomalous behavior. The workflow will reach out to the user who shared the file to check in with them, before removing the share. After this, the security team is noticed.
Again, not all employees mean harm. They simply can be uneducated or not have security in mind. In this scenario, when a user violates a policy:
- They are immediately notified
- They receive guidance on how to remediate the issue
- They are educated on why the behavior is risky
This real-time feedback loop helps:
- Reduce negligent behavior
- Reinforce security best practices
- Build a culture of security awareness
Over time, this leads to fewer incidents and stronger overall security posture.
DoControl recognizes that insider risk management does not exist in isolation. That’s why we integrate with existing tools across your environment: enriching context, strengthening detection, and enabling a more comprehensive approach to SaaS security.
Conclusion
Insider threats are no longer just about people - they’re about identities, behavior, and context. As AI agents and non-human identities continue to operate within SaaS environments, organizations need a new approach to prevention: one that doesn’t just detect risk, but understands and stops it in real time.
There are countless insider risk scenarios that organizations must account for.
- An employee leaving for a competitor may attempt to exfiltrate sensitive data before their departure.
- A third party marketing freelancer could be shared on sensitive customer data for a project, and after engagement ends, they are never unshared from that file.
- A well-meaning employee could make a sensitive file public simply to move work forward more quickly and not get blocked.
- A non-human identity may assume the credentials of a trusted user and quietly download and transfer data to an external system.
- A disgruntled employee may attempt to sell proprietary information to outside entities.
There are so many possible scenarios - and only one security team. For this reason, organizations need an automated, contextual solution that looks at every risk and event in context - and the ability to remediate them at scale.
DoControl delivers exactly that: giving security teams the visibility, context, and control needed to prevent insider-driven data loss before it makes headlines.


.png)
.png)