
Google Gemini is quickly becoming part of everyday workflows. Teams are building and sharing AI-powered assistants to streamline tasks, automate processes, and boost productivity.
But with this rapid adoption comes a new challenge: visibility.
Many of these AI assets - especially customizable ones like Gemini Gems - are being created and shared without the same level of oversight as traditional files. Security and IT teams are often left without clear insight into where these assets live, how they’re being used, or who they’re shared with.
Today, we’re excited to introduce new capabilities in DoControl that bring visibility, control, and automation to Google Gemini Gems - so you can manage them with the same confidence as the rest of your data.
What Are Google Gemini Gems?
Google Gemini Gems are customizable GPTs built within Gemini that users can create as personal assistants, shaped by their own content, knowledge, and structure. Users create task-specific AI chatbots by combining instructions with supporting materials such as documents, PDFs, and internal data.
Instead of starting from scratch each time, users can create a “Gem” with predefined instructions, context, and supporting materials - turning Gemini into a purpose-built assistant for things like content creation, analysis, or internal workflows.
You can think of Gems as:
- Reusable AI workflows
- Task-specific AI agents
- Customized versions of Gemini designed for repeatable use cases
What Powers a Gem
What makes Gems especially powerful is that they’re not just driven by prompts - they can also be trained on files, PDFs, and internal data.
Teams can upload supporting materials such as:
- Product documentation
- Internal guides and playbooks
- Knowledge base articles
- Sensitive business data
These materials help the Gem generate more accurate, contextual, and useful responses.
Where Gems Live, and What That Implies
Gems are stored as files in Google Drive, meaning they can be shared like any other document.
But there’s an important nuance:
For a Gem to function properly, the underlying files and data it relies on must also be accessible to the user interacting with it.
In other words, sharing a Gem often means sharing the data behind it.
The Risk Behind the Gems
As organizations adopt Gemini Gems, they’re not just creating AI assistants - they’re packaging and operationalizing internal knowledge.
And that introduces a new, often overlooked data risk.
Because Gems rely on underlying files and data to function, sharing a Gem externally can unintentionally require sharing the sensitive materials that power it.
This means that even if users don’t have access to the source data, the Gem could still surface sensitive information through the interaction.
A Real-World Example
Imagine an IT company that creates a Gem to help partners learn about its product.
To make the Gem effective, the company uploads:
- Confidential product documentation
- Internal enablement materials
- Detailed technical guides
The Gem works beautifully - partners can ask questions and get accurate, helpful answers.
But behind the scenes, there’s a problem:
To enable this experience, those same partners need access to the attached files that the creator used to train the Gem.
What started as a productivity tool has now created a data exposure risk:
- Sensitive materials are shared externally
- Access expands beyond intended boundaries
- Visibility into this exposure is limited
Why This Is a Growing Security Gap
Security and IT teams face several challenges:
- No centralized visibility into Gems: It’s difficult to identify where Gems exist and what data they rely on
- Hidden dependencies on sensitive data: Gems may be powered by confidential files that aren’t obvious at first glance
- Untracked external sharing: Sharing a Gem can lead to broader data access, but that chain of exposure is hard to monitor
- Lack of real-time awareness and response: Teams may not know when sensitive, Gem-related data is shared externally
As AI-powered workflows become more common, this creates a new class of risk - where sharing an AI assistant can quietly result in sharing the data behind it. Without proper visibility and control, organizations risk exposing critical information without realizing it.
The Solution: DoControl Brings Gemini Gems Into Your Asset Inventory
To address the growing risks around Gemini Gems and their underlying data, DoControl now brings full visibility and control to these AI-powered assets - directly within your existing asset inventory!
With this update, Gemini Gems are no longer a blind spot.
Instead, they are treated like any other governed asset in your environment, giving security and IT teams the ability to discover, monitor, and take action with confidence.
Gems as First-Class Assets
DoControl now recognizes Gemini Gems as files within Google Drive and incorporates them into the asset inventory.
This means teams can:
- Identify where Gems exist across the organization
- Understand their sensitivity, sharing status, and when they were last modified
- Manage them using the same workflows and policies as other critical assets
By bringing Gems into a familiar governance framework, teams gain immediate control over a previously unmonitored surface area.
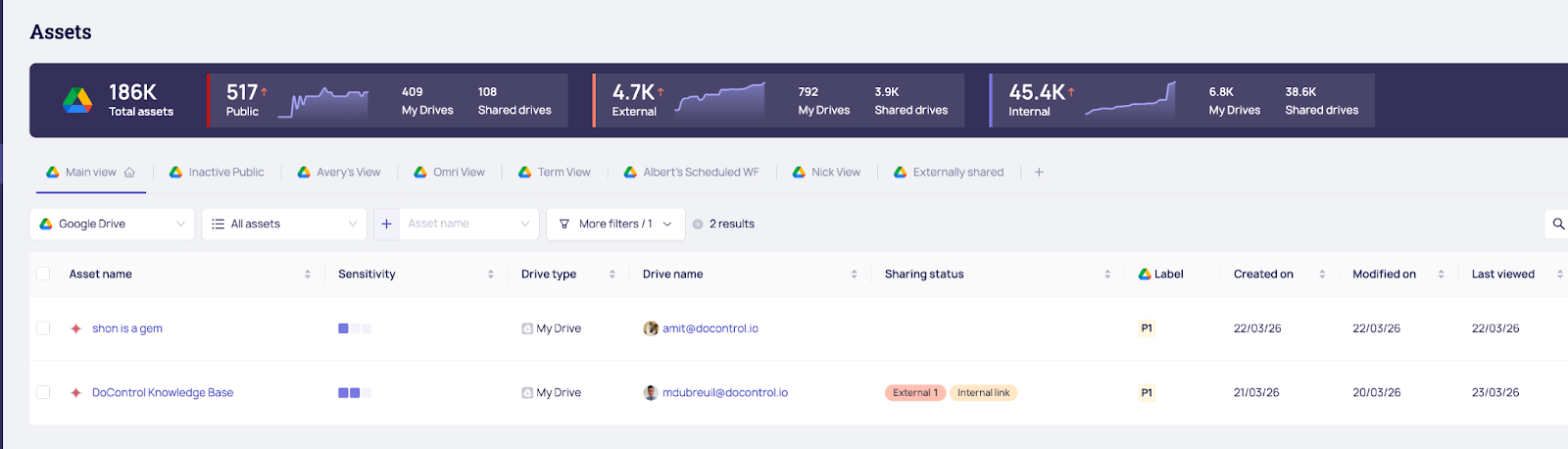
Visibility Into Sharing and Exposure
With Gems now visible in the asset inventory, teams can clearly see:
- All events surrounding the Gems, whether it was a view, access, edit, share, download, etc.
- Which Gems are shared internally vs. externally
- Who has access to them and what they’re doing with them
- Where potential exposure risks exist
This is especially critical given that sharing a Gem may also imply access to the sensitive files behind it.
Actionable Control, Not Just Insight
Visibility is only part of the solution - teams also need the ability to act.
DoControl enables organizations to:
- Quickly remediate risky sharing configurations
- Adjust access permissions directly
- Reduce exposure without disrupting workflows
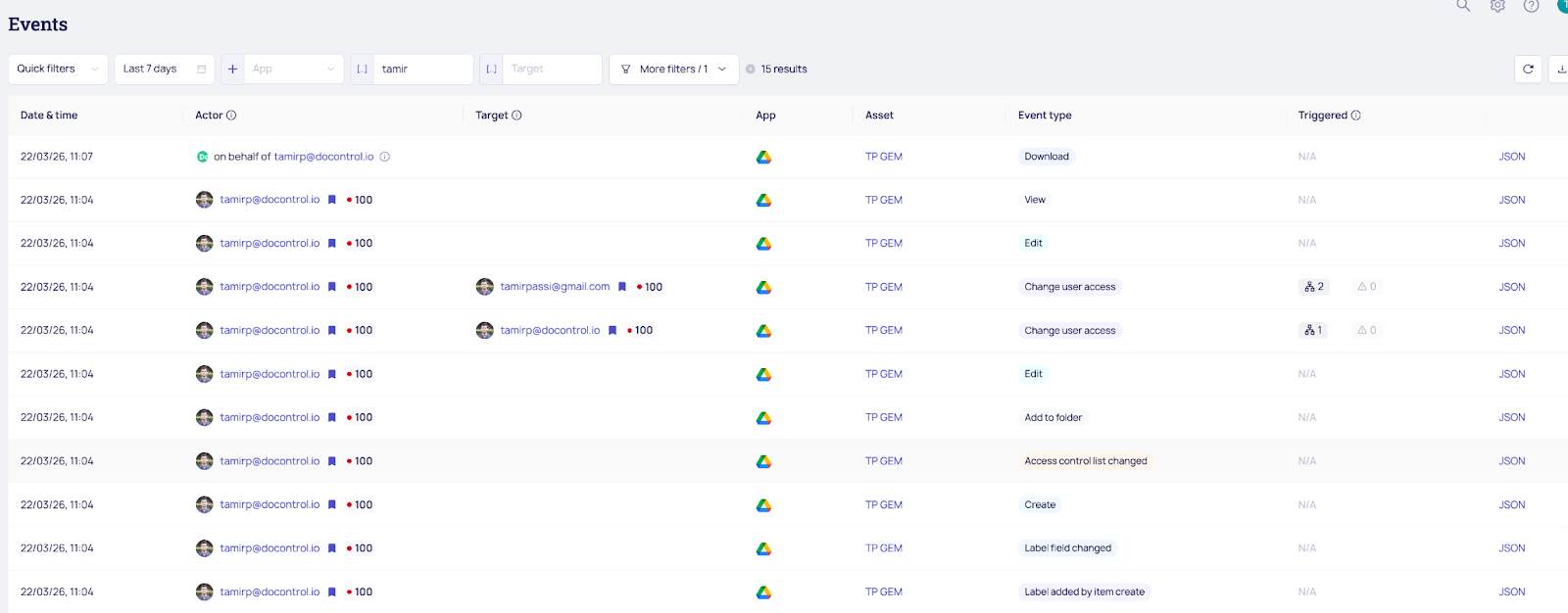
Monitoring What Matters: Gem Sharing Events
Gems are considered as files in Google Drive. Therefore, when a Gem is shared externally, it triggers a:
user access change event with doc_type = gem
This allows teams to:
- Detect when an internal user shares a Gem externally
- Understand when and how Gems are being exposed
- Maintain an audit trail of critical activity
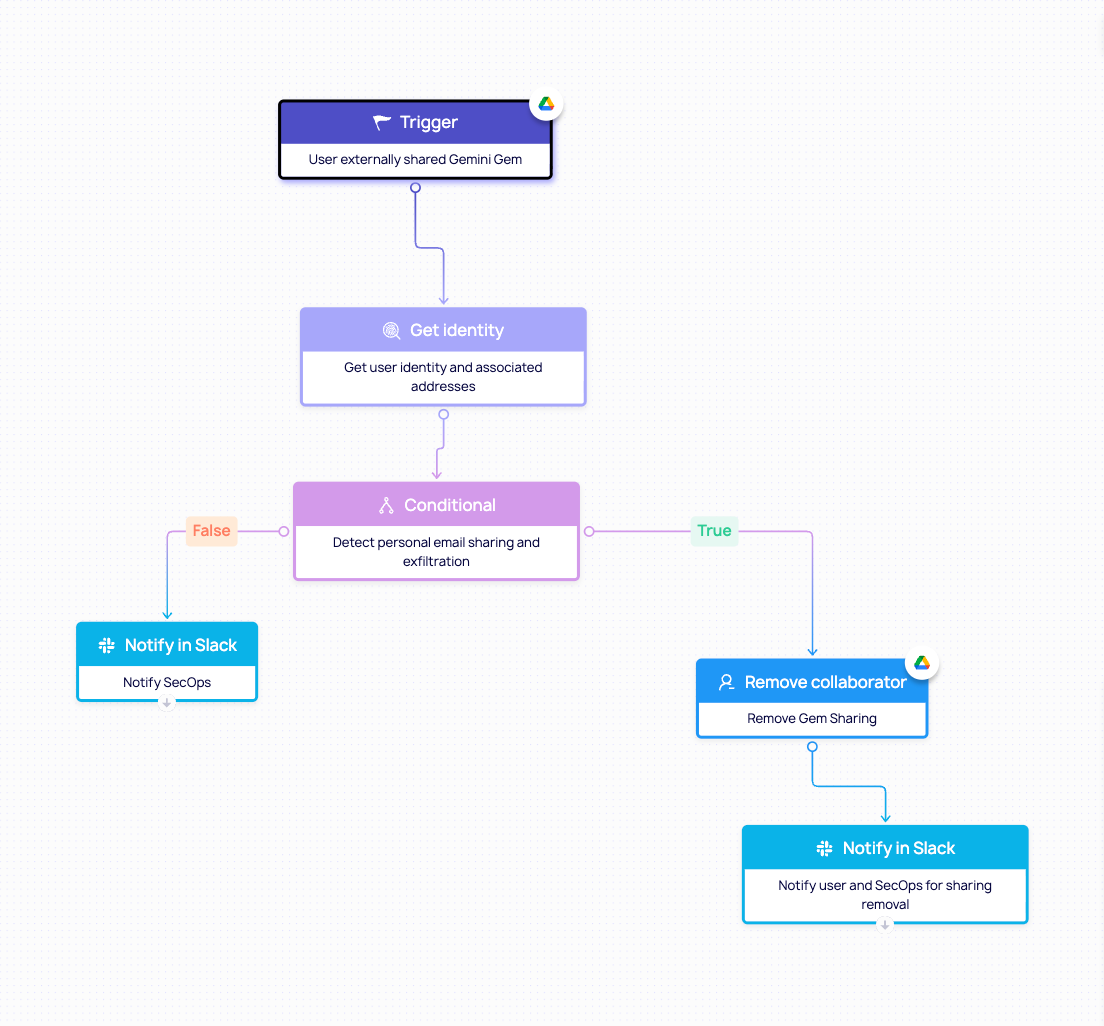
Automating Response at Scale
With these events in place, organizations can go beyond manual monitoring and automate their response.
Teams can trigger workflows to:
- Alert security teams when a Gem is shared externally
- Automatically review or revoke access
- Enforce policies around AI asset sharing
This workflow illustrates what happens when a user externally shares a Gem. DoControl retrieves the user’s identity and associated context, then analyzes the activity to determine whether a personal email is involved or if there are any signs of data exfiltration.
If no risks are detected, SecOps is notified. If a risk is identified, the external collaborator is removed from the Gem, and both the user and SecOps are notified - promoting awareness and reinforcing ongoing security best practices.
Key Takeaway: Why This Matters
AI-powered tools like Gemini Gems are quickly becoming embedded in how modern teams work - transforming how knowledge is created, shared, and operationalized.
But as this shift happens, the definition of “sensitive data” is evolving.
It’s no longer just about individual files. It’s about how those files are packaged, connected, and exposed through AI-driven workflows.
Gems represent a new layer of risk:
- They bundle internal knowledge into reusable systems
- They rely on underlying data that may be sensitive
- And when shared, they can extend access far beyond what’s immediately visible
Without the right visibility and controls, organizations risk exposing not just a single document, but entire collections of proprietary information powering these AI assistants.
With DoControl, teams can stay ahead of this shift.
By bringing Gemini Gems into the asset inventory, enabling real-time monitoring of sharing activity, and automating response workflows, organizations can confidently adopt AI - without sacrificing security.
Because as AI changes how we work, governance needs to evolve with it.
{{cta-1}}



