
Kraken, one of the longest-standing and most security-focused cryptocurrency exchanges, is at the center of a recent cybersecurity incident - not due to a system breach, but because of something far more difficult to defend against: insider access abuse.
The company revealed it is currently facing an extortion attempt tied to two internal security incidents involving unauthorized access to limited customer data.
While Kraken maintains that no funds were ever at risk and its systems were never breached, the incident highlights a rapidly growing threat vector across crypto and fintech: insider-driven attacks.
TLDR;
- Kraken disclosed that a criminal group is attempting to extort the company by threatening to release videos of internal systems.
- Kraken claims that no breach ever occurred, no funds were ever at risk, and it was just threats by a hacker group.
- However, there were two insider-related incidents involving unauthorized access to limited support data that affected roughly 2,000 client accounts.
- Kraken notified its impacted users, tightened controls, and is working with law enforcement on potential arrests.
Who is Kraken?
Founded in 2011 and operated by Payward Inc., Kraken is a U.S.-based cryptocurrency exchange offering spot and derivatives trading, custody, and staking services. The platform serves millions of retail and institutional clients globally and has built a reputation for strong security practices and regulatory compliance.
That reputation makes this incident particularly notable - not because of its scale, but because of how it happened.
What Happened?
According to Kraken’s Chief Security and Information Officer, Nick Percoco, the company identified and contained two separate incidents involving inappropriate access to internal support systems.
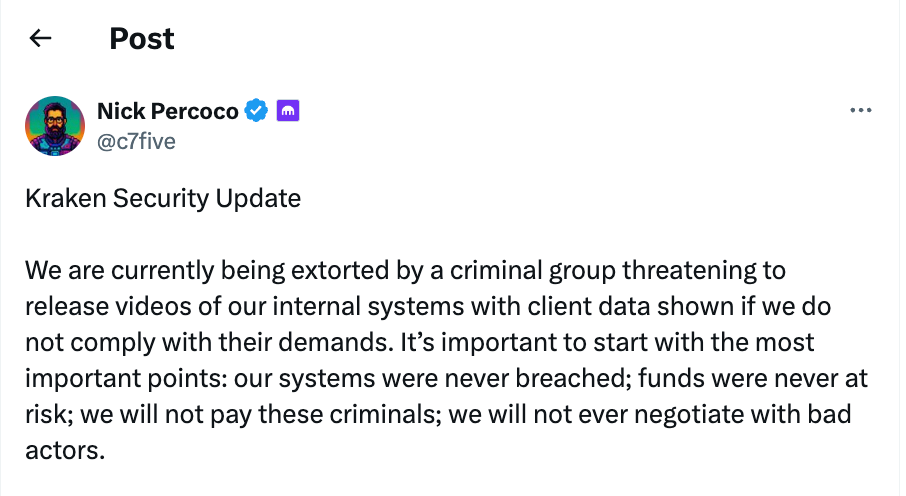
In a public statement shared on X, Percoco emphasized:
“Our systems were never breached; funds were never at risk; we will not pay these criminals; we will not ever negotiate with bad actors.”
Percoco went on to announce that the first incident occurred in February 2025 after Kraken received a tip about a video circulating on a criminal forum that appeared to show access to internal systems. An internal investigation identified a member of the support team as responsible, and their access was immediately revoked.
A second, similar incident occurred more recently, again triggered by an external tip and involving another individual with internal access. In both cases, Kraken:
- Revoked access immediately
- Conducted full investigations
- Implemented additional security controls
- Notified affected users
Across both incidents, approximately 2,000 customer accounts (0.02% of Kraken’s user base) were potentially viewed, with exposure limited to support-related data.
The Extortion Attempt
Shortly after the second incident was contained, Kraken began receiving extortion demands.
The attackers claim to possess videos showing internal system access and have threatened to release the materials publicly on social media and to media outlets unless their demands are met.
Percoco went on to explain how no breach occurred; “Based on intelligence gathered across both incidents, along with extensive ongoing analysis, we believe there is sufficient evidence to support the identification and arrest of those responsible.”
The company is now working with law enforcement and industry partners, and believes there is sufficient evidence to identify and arrest those responsible.
How the Incident Happened: The Insider Threat Vector
This was not a traditional cyberattack involving exploited vulnerabilities or compromised infrastructure.
Instead, both incidents were rooted in insider-related access misuse - either through malicious intent, coercion, or external recruitment of employees.
Why Crypto Companies Are Especially at Risk
The crypto industry presents a uniquely attractive environment for attackers:
- High-value, liquid assets that can be moved instantly
- Irreversible transactions, making recovery nearly impossible
- Complex infrastructure, including exchanges, custody systems, and DeFi protocols
- Heavy reliance on internal tools and support systems
Even firms with strong external security postures are vulnerable if insider access is not tightly controlled and continuously monitored.
Why Traditional Security Models Fall Short
Most security architectures are built around a fundamental assumption:
If a user is authenticated, they can be trusted.
But insider-driven incidents like the one at Kraken expose the limitations of that model.
Traditional security controls are designed to answer a binary question:
“Should this user have access?”
What they fail to answer is far more important:
“Is this access appropriate, at this exact moment, given the context of this person's role, scope, and usual behavior?”
The Lack of Nuance in Access Control
In most organizations, access is granted based on roles or groups:
- Support agents can access customer data
- Engineers can access internal systems
- Analysts can query datasets
Once access is granted, it is often:
- Broad
- Persistent
- Largely unmonitored in real time
This creates a critical blind spot. An employee operating fully within their assigned role may:
- Access sensitive customer data
- View internal systems
- Interact with critical infrastructure
And from a traditional security perspective, this activity appears completely normal.
The Missing Context Problem
It could appear normal. But things aren’t always as they seem. The issue is not access itself - it’s the lack of context around how access is used.
Traditional controls cannot distinguish between:
A support agent accessing a customer account to resolve a ticket vs. a support agent accessing an account that they plan to exfiltrate data from
This scenario technically falls within “authorized access” - but only one represents legitimate business activity. Without context, security systems treat them the same.
Why This Matters in Insider Incidents
In the Kraken case, the individuals involved did not need to “break in.” They already had access. The risk emerged from:
- How that access was used
- What data was being viewed
- Whether the behavior aligned with expected workflows
This is where traditional controls break down:
- They do not baseline normal behavior at a granular level
- They do not detect subtle deviations within allowed access
- They do not trigger alerts based on intent or anomaly
This creates a false sense of security where organizations believe they are protected because:
- Access is restricted
- Authentication is enforced
- Permissions are defined
But in reality, authorized users can still perform unauthorized actions - without triggering any alerts.
Even worse, overly rigid controls can create the opposite problem:
- Security teams hesitate to tighten access for fear of disrupting operations
- Broad permissions remain in place “just in case”
- Risk accumulates silently over time
The Bottom Line
Traditional security models are effective at keeping external attackers out.
But they are not designed to:
- Understand user intent
- Evaluate behavioral risk
- Differentiate between normal and abnormal use of data
And as the Kraken incident demonstrates, that’s exactly where today’s attacks are happening.
How DoControl Closes the Context Gap in Modern Security
The failure exposed in the Kraken incident was not a lack of access controls - it was a lack of contextual understanding of how access was being used.
This is where modern platforms like DoControl fundamentally change the security model.
Instead of asking:
“Does this user have access?”
DoControl continuously evaluates:
“Is this access behavior appropriate, expected, and safe—right now?”
From Static Access to Context-Aware Access Governance
Traditional systems grant access once and assume it will be used appropriately.
DoControl introduces data access governance that continuously evaluates:
- Who is accessing data
- What data is being accessed
- When and how often
- In what context (workflow, ticket, task, or anomaly)
This allows organizations to distinguish between:
- A support agent resolving a legitimate customer issue
- A support agent accessing accounts outside of any defined workflow
The difference is not permissions - it’s context.
Detecting Risk Within “Normal” Behavior
In insider-driven incidents, risky activity often hides inside what appears to be normal access.
DoControl’s Insider Risk Management capabilities establish behavioral baselines and detect:
- Deviations from typical access patterns
- Unusual spikes in sensitive data access
- Access that does not align with business workflows
- Subtle indicators of compromised or recruited insiders
This enables security teams to catch misuse of legitimate access - not just unauthorized access
Identity Threat Detection Beyond Authentication
Authentication alone cannot determine whether a user is acting maliciously.
DoControl’s Identity Threat Detection & Response (ITDR) layer continuously assesses identity risk by analyzing:
- Behavioral anomalies across SaaS and internal systems
- Signals of account compromise or coercion
- Risky access patterns tied to specific identities
When risk is detected, DoControl can:
- Trigger real-time alerts
- Automatically revoke or limit access
- Initiate remediation workflows
This ensures that trusted identities do not become silent attack vectors.
Dynamic, Context-Aware Access Enforcement
Rather than relying on static roles and over-permissioned access, DoControl enforces:
- Dynamic least-privilege access based on real-time context
- Just-in-time access controls for sensitive data
- Automated remediation workflows that respond to any sort of insider risk scenario, ranging from broad, generic policies to nuanced, multi-step processes
This means access is no longer binary (allowed vs. denied), but continuously evaluated and adjusted based on behavior and risk.
Preventing Data Exposure and Exfiltration
In incidents like Kraken’s, the risk is not just access - but what happens to the data after it is accessed.
DoControl provides deep visibility and control over:
- Sensitive data access across SaaS applications
- What users are doing with the data
- Internal and external data sharing
- Potential exfiltration paths
It can automatically:
- Block unauthorized sharing
- Revoke permissions
- Restrict data movement
- Tag in security teams or response teams when needed
- Contain exposure before it escalates into a breach or extortion scenario
Full Visibility, Faster Response
Perhaps most critically, DoControl eliminates the visibility gap that allows insider threats to go undetected. AND, can actually control and remediate the risk in real time.
Security teams gain:
- A complete, real-time view of data access across the organization
- Clear attribution of who accessed what, when, and why
- Automated remediation, investigation, and response workflows
This reduces:
- Time to detection
- Time to containment
- Overall impact of insider-driven incidents
The Bigger Picture
The Kraken incident is not an anomaly, it’s a signal.
As external defenses improve, attackers are shifting inward, targeting employees, contractors, and support personnel with legitimate access to critical systems.
Security is no longer just about controlling access - it’s about understanding and governing how access is used.
DoControl enables organizations to move from:
- Static permissions → Dynamic, context-aware governance
- Blind trust → Continuous verification & evaluation based on context
- Reactive response → Proactive risk prevention
The question is no longer:
“Can we prevent breaches?”
But rather:
“Can we control and monitor how our data is accessed from within?”
Kraken successfully contained the incident, protected client funds, and responded decisively to extortion attempts. But the underlying lesson is clear:
Insider risk is now one of the most pressing security challenges, and its time to adapt.



