Global SaaS spending is expected to reach nearly $300 billion by the end of the year - making SaaS not just a trend, but the foundation of modern business operations.
But as SaaS adoption grows, so does the risk of data loss. Data is no longer confined to a network perimeter. Instead, it moves freely between:
- Internal employees
- Shared drives
- External collaborators
- Third-party vendors, contractors, & agencies
- Third-party apps & integrations
- Non-human identities (NHIs)
- AI agents interacting directly with enterprise data
SaaS platforms are designed to make sharing and collaboration seamless. But at the same time, a single click can expose sensitive data externally, publicly, or even permanently.
This creates a critical challenge:
Organizations no longer just need to protect data, they need to control how it moves.
This is where Data Loss Prevention (DLP) becomes essential.
At a high level, effective DLP in SaaS environments enables organizations to:
- Identify where sensitive data exists across applications
- Understand how that data is being accessed, shared, stored, and moved
- Detect risky behaviors such as unauthorized sharing, downloads, or exports
- Prevent data from being exposed, leaked, or exfiltrated
- Continuously enforce policies without disrupting business operations
Modern organizations need a new approach to DLP - one that is dynamic, identity-driven, and context-aware.
In this article, we’ll explore:
- What DLP today
- Why it has become critical in modern SaaS environments
- Emerging trends shaping the future of DLP
- How DoControl approaches DLP and helps organizations secure SaaS data at scale
What Is Data Loss Prevention (DLP)?
At its core, Data Loss Prevention (DLP) is a set of strategies and technologies designed to prevent sensitive data from being exposed, leaked, or accessed by unauthorized entities.
It answers a fundamental question:
Is sensitive data being used, shared, or moved in a way that puts the organization at risk?
In SaaS environments, DLP goes beyond simply identifying sensitive data. It provides visibility into:
- Where sensitive data lives
- Who has access to it
- Why they have access to it
- How it is being used
- When and where it is being accessed
- How it is being shared, downloaded, or exported
This visibility is critical, but visibility alone is not enough, because:
Visibility ≠ protection.
Seeing you have risks doesn't fix them. As a result, a modern DLP strategy must also enable organizations to take action.
Why DLP is More Critical Than Ever
Sensitive data is now distributed across hundreds of applications, accessed by a mix of human and non-human identities, and constantly moving between internal and external environments. Traditional approaches to data protection can no longer keep up.
Below are the key factors driving the need for modern SaaS DLP:
1. SaaS Sprawl
Organizations today rely on an ever-expanding number of SaaS applications. According to Gartner, the average organization uses over 125 SaaS applications - many of which operate outside of IT’s visibility.
Each application introduces another surface for potential data exposure, making it increasingly difficult to track where sensitive data lives and how it is being accessed.Therein lies the compounding issue of SaaS sprawl.
2. Oversharing and Public Exposure
SaaS platforms are designed for easy collaboration, but that convenience often leads to overexposure. Public sharing links frequently remain active long after they are needed, leaving sensitive data accessible to anyone with the link.
In the recent Scale AI incident, for example: files set with “Anyone with the link can view,” sharing permissions started a deadly data breach - exposing thousands of files covering proprietary AI training materials, employee performance ratings, customer PII, confidential manuals belonging to Google and Meta, and more.
3. Third-Party AI and Shadow Applications
Employees regularly connect third-party applications and integrations to core SaaS platforms such as Google Workspace and Slack. Many of these applications operate outside of IT’s oversight and are often granted excessive permissions, allowing them to access, modify, or export sensitive data.
These “shadow apps” - many of now are GenAI shadow apps or have agentic AI capabilities embedded within them - create significant blind spots and increase the risk of unintended data exposure.
4. Insider Risk
95% of incidents happen due to human error. Employees - whether due to human error or lack of awareness - can unintentionally expose sensitive data by sharing files with the wrong audience, uploading restricted information to public channels, or granting excessive access permissions.
At the same time, malicious insiders or departing employees may intentionally exfiltrate data up until their final departure date. Insider risk manifests itself in many forms. This makes it critical to monitor behavior and apply context to ALL data access - 100% of the time
5. AI and Autonomous Agent Risk
The rapid adoption of AI tools - such as Gemini, Claude, Microsoft Copilot, and Glean - is introducing entirely new data exposure pathways. These AI tools and agents are rapidly being integrated into enterprise workflows. When AI systems interact with organizational SaaS data, companies often have little visibility into what those systems are doing with it.
If an AI agent downloads data into a workspace, an account becomes compromised, or sensitive information is exported outside the environment, organizations can quickly lose control of their data and expose themselves to significant risk. In Microsoft, it was analyzed that approximately 70% of all actions were taken by non-human identities (NHIs) rather than by human users, and in Google Drive environments, this percentage was 40%.
6. Compromised Accounts and Third-Party Takeovers
When user accounts or third-party integrations are compromised, attackers inherit the same permissions as legitimate users. Increasingly, NHIs are becoming one of the fastest paths to compromise. Many security teams lack visibility into the AI agents and integrations operating within their environments, creating blind spots that attackers can exploit.
Account compromise remains one of the most critical concerns for security teams because once access is gained, it can be extremely difficult to detect and remediate in time. This allows attackers to directly access, download, and exfiltrate sensitive data from SaaS applications with little resistance.
Emerging Trends Shaping DLP
Modern SaaS DLP must account for new actors, new behaviors, and new risks.
Three major trends are reshaping how organizations approach data loss prevention today:
1) Non-Human Identities (NHIs)
As mentioned previously, not all data access in SaaS environments comes from human users.
Automation tools, third-party integrations, APIs, and service accounts - collectively known as non-human identities (NHIs) - now account for a significant portion of activity across SaaS applications.
These identities often:
- Operate continuously in the background
- Have persistent, and often excessive, permissions
- Interact with large volumes of sensitive data
- Lack the same level of visibility and governance as human users
In many cases, organizations don’t even have a complete inventory of the NHIs operating within their environment. This creates a critical risk.
If an NHI is misconfigured, over-permissioned, or compromised, it can access, move, and expose sensitive data at scale - often without triggering traditional security controls.
As a result, modern DLP strategies must extend beyond users and include full visibility and governance over non-human identities.
2) Agentic AI and Autonomous Systems
Similar to the last trend, AI is rapidly becoming embedded into SaaS environments.
From copilots to workflow automation tools, agentic AI systems are now capable of independently accessing, processing, and moving data across applications.
These systems introduce a new category of risk:
- AI agents can access sensitive datasets to generate outputs
- They can move data across systems without direct human interaction
- They can unintentionally expose sensitive information through generated content
- They can operate at a scale and speed that far exceeds human activity
Unlike traditional users, AI agents are programmatic and autonomous, making their behavior harder to predict and control.
Without proper governance, organizations risk losing visibility into how sensitive data is being used - and where it is ultimately going.
This makes it critical for DLP solutions to monitor and control not just human behavior, but AI-driven interactions with data.
3) The Growing Importance of Context
As environments become more dynamic, context has become the defining factor in effective data loss prevention.
Traditional DLP solutions rely heavily on static rules - such as blocking downloads or flagging certain file types. But in SaaS environments, these actions are often part of normal business operations.
A file download, a share, or an export is not inherently risky. What matters is the context surrounding that action:
- Who is performing the action
- What data is being accessed
- Where the access is coming from
- When the activity is taking place
- Why the action is occurring
Without this context, organizations are left with two bad options:
- Overly restrictive controls that disrupt business
- Or overly permissive policies that allow risk to go undetected
Modern DLP requires a context-driven approach; one that can distinguish between legitimate activity and true data loss risk. This is what enables organizations to protect sensitive data without slowing down the business.
How DoControl Solves for SaaS Data Loss Prevention
DoControl was built to solve one of the most critical challenges in modern SaaS environments: preventing sensitive data from being exposed, leaked, or exfiltrated - without slowing down the business.
Traditional DLP solutions focus on detection. They generate alerts, flag policies, and surface potential risks - but often stop short of actually preventing data loss.
DoControl takes a different approach.
We combine deep visibility, contextual understanding, and automated remediation to not only identify risk, but actively prevent data loss in real time.
Visibility without control is meaningless, and unfortunately, many solutions promise protection, but stop at alerts and dashboards.
DoControl goes further: delivering the visibility organizations need, along with the remediation capabilities and control required to actually prevent data loss across SaaS environments.
DoControl approaches SaaS DLP through six core capabilities:
1. SaaS Data Discovery and Sensitive Data Identification
You can’t prevent data loss if you don’t know where your sensitive data lives.
DoControl automatically discovers and inventories data across connected SaaS applications, including:
- Files and documents
- Shared drives and repositories
- Messages and records
- Users and collaborators
- OAuth applications and integrations
- Metadata and activity events
In addition, DoControl identifies sensitive data across these environments - such as financial information, customer data, intellectual property, and regulated data. This foundational layer gives organizations a complete view of their SaaS data footprint, eliminating blind spots and enabling effective DLP.
2. Data Exposure Analysis and Risk Prioritization
Once sensitive data is identified, DoControl evaluates how that data is being exposed and where risk exists. The platform analyzes:
- External and public sharing
- Data shared with personal email accounts
- Third-party and external collaborator access
- Large downloads or unusual export activity
- Over-permissioned access
Each asset is assigned a risk and sensitivity profile, allowing security teams to prioritize the most critical data exposure risks.
This ensures teams can focus on what actually matters, rather than being overwhelmed by noise.
3. Context-Aware DLP Controls
One of the biggest challenges in DLP is distinguishing between normal data movement and true data loss. DoControl solves this through context-driven controls.
DoControl integrates with HRIS and IdP systems to gather all context on users: role, department, behavioral baselines, historical activity patterns, risk insights, and more. Instead of relying on rigid, static rules, DoControl evaluates:
- Who is accessing the data
- What data are they touching
- Does that activity make sense in context, relative to their role, scope, and normal behavior?
This allows organizations to:
- Prevent risky data sharing without blocking legitimate collaboration
- Detect anomalous downloads or exports
- Identify when sensitive data is being accessed outside normal patterns
Context is what transforms DLP from reactive to intelligent.
Here’s a quick example:
Imagine a marketing manager sharing customer data with an external growth agency. On its own, this action is completely normal - agencies often need access to this type of data to do their job. But now consider a different scenario.
That same marketing manager suddenly shares that same file with a personal email address late at night, shortly after switching departments, and putting in their two weeks.
DoControl’s DLP engine connects contextual signals like role changes or resignation with abnormal activity spikes.
4. Identity-Driven Data Loss Prevention
In SaaS environments, data loss is almost always tied to identity.
DoControl provides deep visibility into:
- Human identities (employees, contractors, vendors)
- Non-human identities (AI agents, OAuth apps, service accounts)
- Access privileges across SaaS platforms
- Identity behavior and risk signals
This is especially critical as NHIs and AI agents increasingly interact with sensitive data.
If an identity - human or non-human - is compromised or behaving abnormally, DoControl can immediately detect and respond to prevent data loss.
5. Automated Data Loss Prevention at Scale via Workflows
Detection without action is not DLP. DoControl equips organizations with powerful remediation capabilities to stop data loss as it happens. This is the core of our product and our key differentiator - as it is what truly enables us to protect SaaS data for all of our customers.
Remediation with DoControl can be performed in two primary ways:
Bulk remediation at scale
When organizations first onboard with DoControl, there is typically a large backlog of existing exposure risks - such as:
- Publicly shared files
- Data shared with external domains
- Over-permissioned access
- Sensitive data exposed unintentionally
These risks are identified during a Free Risk Assessment or Proof of Value (POV).
From there, security teams can remediate large volumes of assets in bulk, quickly reducing exposure across their environment.
Automated workflows that run 24/7
Once initial cleanup is complete and companies officially partner with DoControl, organizations can implement continuous DLP enforcement through automated workflows.
DoControl provides pre-built playbooks, while also allowing customers to create custom workflows tailored to their policies.
These workflows can automatically:
- Revoke public sharing links
- Remove unauthorized external collaborators
- Block or reverse sensitive file sharing
- Detect and stop large or anomalous downloads
- Revoke high-risk OAuth integrations
- Time-box access to sensitive data
- Trigger alerts or escalation based on risk signals
…and much more. Customers can essentially create a workflow for any scenario they desire, and engage managers or security team members to approve actions via Slack or Gmail to ensure business ops keep flowing..
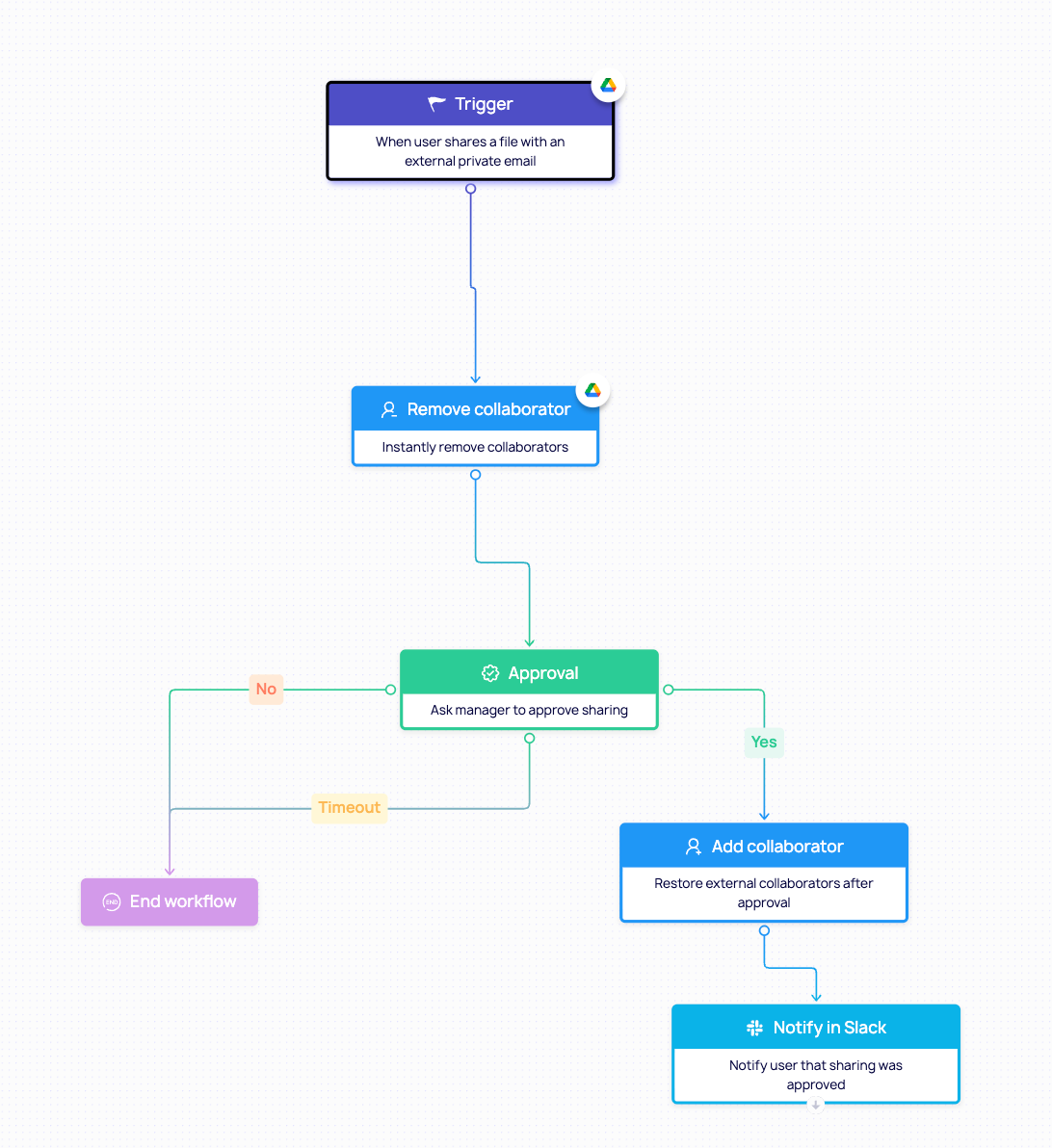
Here’s an example of a workflow that removes external collaborators from a file. In this workflow, a manager is looped in to deny or approve the sharing,. If they allow it, the external collaborator will be restored. This is just one example of how flexibility and business enablement is a key pillar of our DLP workflow engine.
6. Leveraging Data Classification and Metadata (Google Labels)
DoControl enhances DLP by leveraging existing data classification and metadata signals from SaaS platforms such as Google Workspace.
This includes:
- Google Drive labels
- File metadata
- Ownership and access history
- Organizational roles
By integrating these signals into policies, organizations can:
- Apply DLP controls based on data sensitivity
- Automatically enforce rules on classified data
- Improve accuracy and reduce false positives
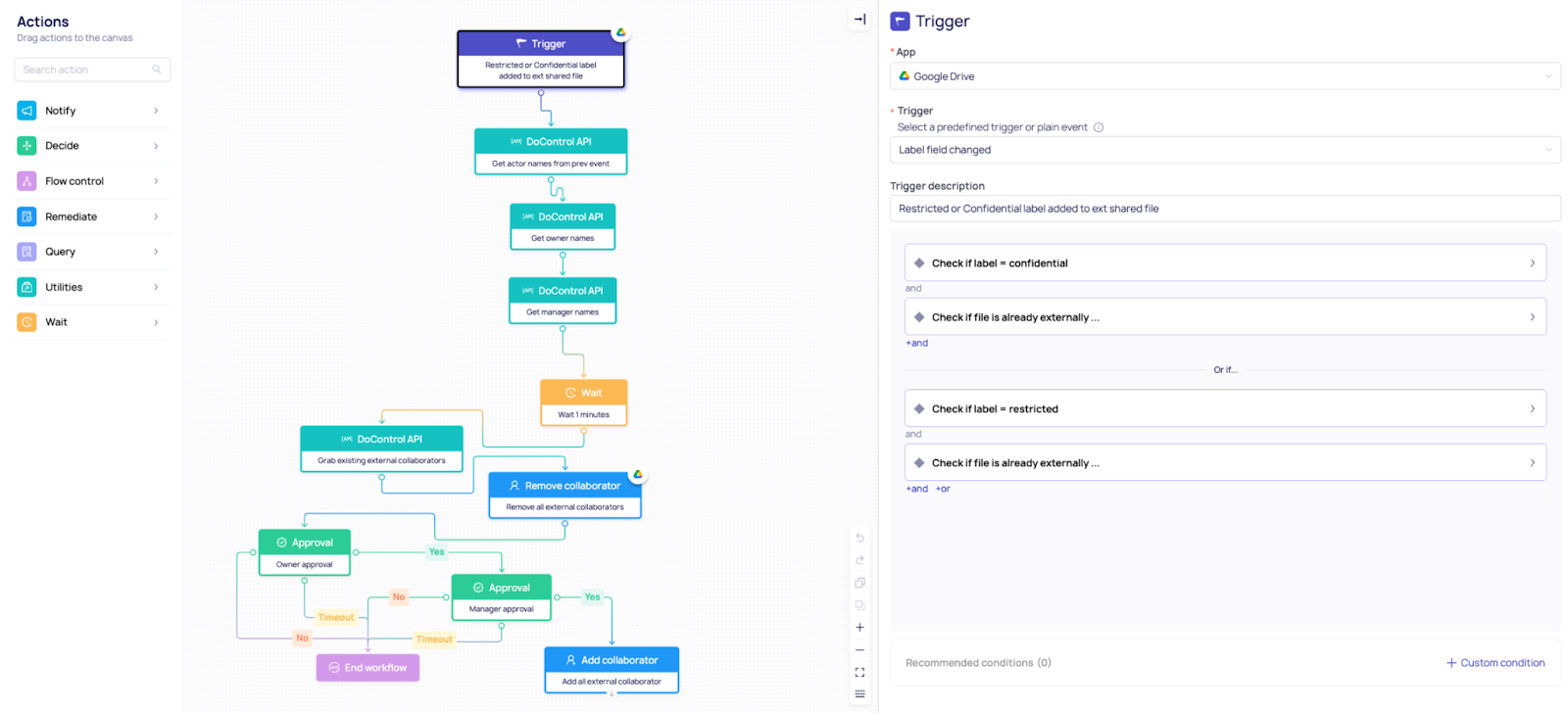
Here’s an example of a workflow that does a similar job to the above workflow - but this one leverages Google labels to classify data first.
In this example, our DLP workflow engine pulls the labels already created in the customer’s Google Workspace environment. It then removes collaborators, requests manager approval, and removes and/or adds the collaborator back as needed.
DoControl recognizes that different solutions address different security challenges.
That’s why we integrate with existing tools across your environment - enriching context, strengthening enforcement, and enabling organizations to build a comprehensive, layered approach to SaaS data loss prevention.
Key Takeaway
The way organizations work has changed forever - and so has the way we must protect data.
It’s not just about preventing data loss or leakage; it’s about enabling trust: trust that your information, your people, and your technology can move in a way that protects your critical SaaS data without slowing down business productivity.
The future of DLP is real-time, identity-driven, and context-aware. Organizations need solutions that not only detect risk, but understand it and act on it instantly - all without slowing down the day-to-day operations of the business.
DoControl is leading the charge in this shift: helping companies stay ahead of evolving threats, while maintaining the speed and collaboration that SaaS was built for.