If you're trying to lock down your SaaS environment, you've probably come across two acronyms that seem like they're solving the same problem: SSPM (SaaS Security Posture Management) and CASB (Cloud Access Security Broker).
Both live in the SaaS security space. Both show up in vendor pitches. And both get thrown around interchangeably - even though they aren't the same thing.
This article breaks down what each tool actually does, where they diverge, and how to think about which one belongs in your security stack. Spoiler: for most modern enterprises, the answer isn't either/or.
What Is SSPM?
SSPM (SaaS Security Posture Management) connects directly to your SaaS applications via API and examines what's happening inside them - continuously, across your entire SaaS estate.
SSPM is built to answer a specific question: is the inside of my SaaS environment actually secure? That means looking at permissions, user activity, third-party integrations, shared files, AI integrations, configurations, and identity-level risk.
Where other tools watch the perimeter, SSPM walks through every room in the house and checks whether the windows are locked, the valuables are properly stored, and no one left a spare key under the mat.
Core SSPM capabilities include:
- Data access governance - understanding who has access to what data, how that access was granted, and whether it aligns with policy.
- Data loss prevention (DLP) - maintaining zero trust policies, evaluating data movement and activity in context, and setting up granular access controls to prevent data from being misused or exfiltrated outside the digital walls of the organization.
- Identity and permissions management - mapping access and activity across employees, contractors, service accounts, and non-human identities like AI agents.
- OAuth and third-party app governance - discovering, assessing, analyzing, monitoring, and revoking risky third-party integrations that employees add to the environment.
- Shadow SaaS and shadow AI discovery - surfacing unsanctioned apps connected via OAuth or other signals and remediating them based on risk.
- Configuration and drift monitoring - continuously benchmarking SaaS settings against frameworks like CIS, NIST, and SOC 2, detecting when settings drift from a secure baseline, and remediating them once they drift.
- Automated remediation - not just identifying risk, but closing it: revoking access, removing permissions, correcting misconfigurations automatically through bulk remediation capabilities or automated workflows.
That last point matters more than it might seem. Visibility without remediation is just a longer to-do list. The best SSPM platforms close the loop.
What Is a CASB?
A CASB (Cloud Access Security Broker) sits between your users and their SaaS applications - monitoring and controlling traffic as it flows to and from the cloud. Think of it as a security checkpoint at the front door.
CASBs were built to answer a different question: what are my users doing when they access cloud apps?
They work by inspecting network traffic - either inline (as a proxy) or via API - to enforce policies around access, data transfer, and user behavior. A CASB can block an employee from uploading a sensitive file to a personal Dropbox, flag unusual login activity from an unrecognized device, or prevent access to unsanctioned apps entirely.
Core CASB capabilities typically include:
- Visibility into cloud app usage - which apps employees are accessing, from what devices and locations
- Data loss prevention (DLP) - blocking or alerting when sensitive data is being moved or shared in violation of policy in the cloud
- Access control - enforcing conditional access policies based on device health, location, or user role
- Threat protection - detecting anomalous activity like impossible travel or unusual download volumes
- Shadow IT discovery - identifying unsanctioned apps employees are using without IT approval
CASBs were transformative when they emerged. But they were designed for a different era - one where most SaaS risk came from who was accessing apps, not from what was happening inside them as well.
Where CASB Falls Short in 2026
CASBs haven't gone away - but the threat landscape has evolved in ways that severly expose their limitations.
- They can't see inside the apps.
A CASB can tell you that an employee accessed Salesforce. It can't tell you that a misconfigured sharing setting in Salesforce just made 10,000 customer records visible to anyone with the link.
- They weren't designed for OAuth risk.
The most dangerous integrations in your SaaS environment aren't users uploading files - they're third-party apps that were granted OAuth access years ago and have been quietly accumulating permissions ever since.
CASBs have limited visibility into this attack surface. The recent Vercel data breach is a perfect example: an employee connected an app via OAuth, that app was later compromised, and sensitive data was exfiltrated at scale. A CASB wouldn't have caught it.
- They don't handle non-human identities.
AI agents, copilots, MCP connections, and service accounts now outnumber human users in most enterprises. These identities have their own scopes, their own blast radius, and their own risk profile. CASB architectures weren't built to govern them.
- They generate noise, not context.
Many CASB deployments end up producing high volumes of alerts without the identity, behavior, and data context needed to prioritize them. Security teams burn time chasing false positives rather than closing real risk.
- They remediate at the edge, not at the source.
A CASB can block a file upload in transit. It cannot revoke a misconfigured permission, correct a drifted admin setting, or remove an overprivileged external collaborator from a shared drive. The misconfiguration stays, and so does the risk.
- There is limited API support.
Not all CASBs support every cloud service API, which can limit their effectiveness - especially for organizations and enterprises that are fully operating within SaaS.
- There are severe latency concerns.
Proxy-based CASBs may introduce latency in traffic flow. For example, when there is an event - let’s say a risky share or a burst download - the CASB catches it when it's doing a periodic scan. Well, that periodic scan may happen 2 hours after the event happened. In that case, the data already walked out the door and the breach already occurred.
Where SSPM Directly Addresses Those Gaps
Each of the CASB limitations above has a direct SSPM answer.
- SSPM operates inside the app, not at the edge.
Because SSPM connects via native APIs, it has full visibility into what's happening within the application - sharing settings, permission states, connected integrations, configurations, and user activity logs. It sees what a traffic-layer tool cannot.
- SSPM was built for OAuth and third-party app risk.
SSPM platforms inventory every third-party app connected to your SaaS environment, evaluate their scopes and risk levels, and can automatically revoke integrations that cross policy thresholds.
- SSPM treats non-human identities as first-class citizens.
Modern SSPM platforms inventory AI agents, service accounts, and OAuth-connected apps the same way they handle human users - scoping their access, monitoring their behavior, and applying least-privilege controls at scale. In 2026, this isn't optional coverage. It's the core of the problem.
- SSPM enriches every signal with context.
Rather than raw alerts, SSPM platforms apply identity, behavioral, and data sensitivity context to every finding - surfacing what's actually risky and filtering out the noise. Security teams see fewer alerts, and the ones they do see are actionable and they can prioritize them.
- SSPM remediates at the source (at least, DoControl’s does).
This is where the categories diverge most sharply. SSPM doesn't just flag the issue, the drift, the integration, the external share, the burst download, etc. - it remediates, revokes, and eliminates the risk in real time. Misconfigured sharing setting? Corrected. Dormant OAuth grant? Revoked. External collaborator with lingering access on a sensitive project? Removed. Automatically, at scale, without a ticket queue.
- SSPM's are API-based, and there is no latency.
Unlike CASBs that rely on inline proxies, SSPM platforms connect directly to SaaS applications via API, with no latency and no traffic bottlenecks. DoControl, for example, runs on an event-driven, pull-based architecture - subscribing directly to each SaaS application's event stream. When an action occurs (a file shared externally, an encryption key uploaded, an OAuth scope granted) DoControl receives a notification in near real-time and pulls the event as it happens. That triggers an immediate alert, automated remediation, or policy-driven action, ensuring nothing slips through the cracks.
SSPM vs. CASB: A Direct Comparison
Here's how the two categories stack up across the dimensions that matter most to security teams:
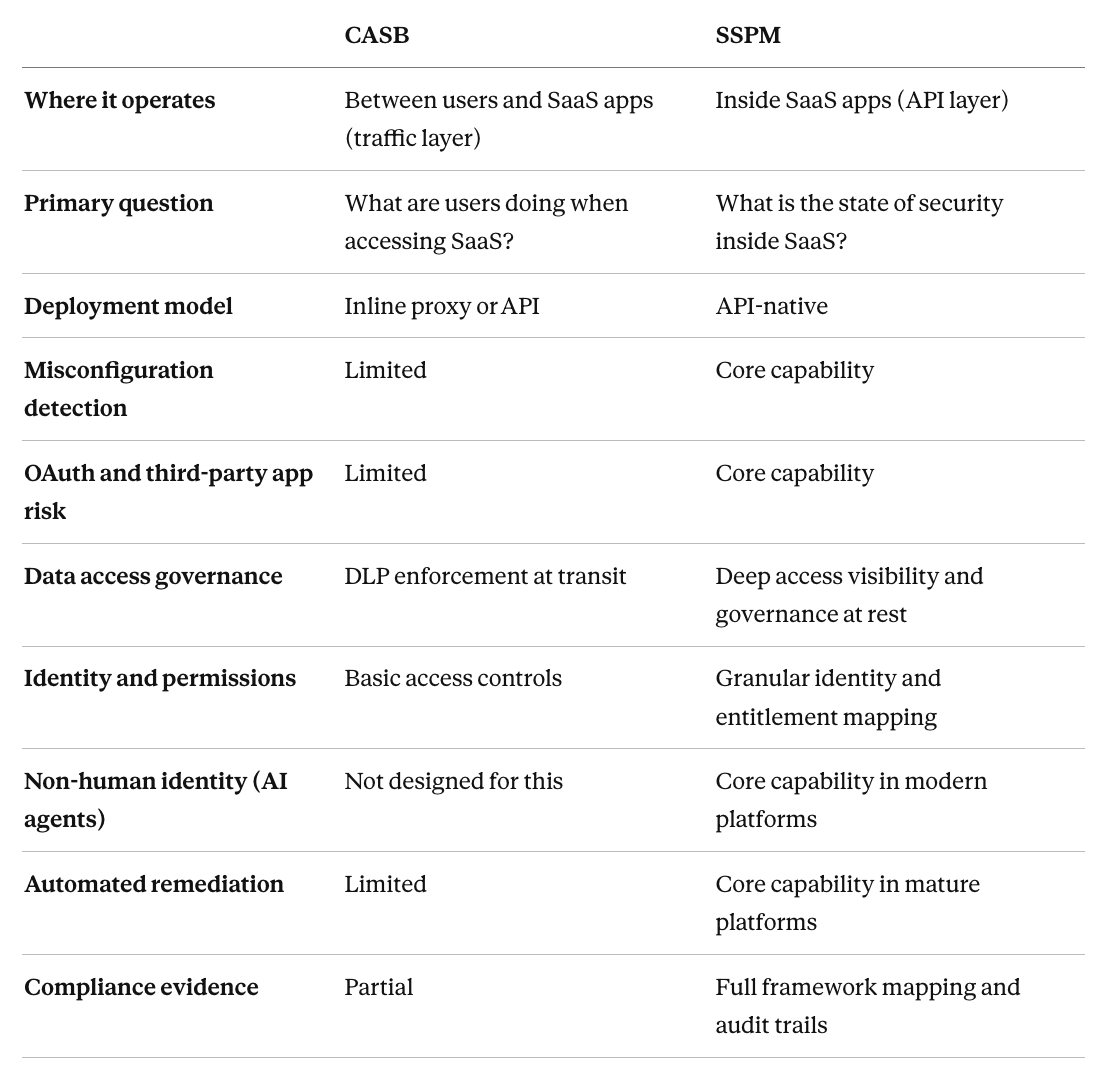
The key point? CASBs are strong at controlling the movement of data. SSPMs are strong at managing the state of your SaaS environment. These are related concerns, but they aren't the same concern.
Do You Need Both?
For many organizations, the honest answer is no - but you need a clear understanding of what each tool is doing. Realistically, your SSPM should also act as an ‘API-casb’ - but with more perks.
A CASB handles traffic-layer controls: blocking uploads, enforcing access policies, inspecting data in motion. An SSPM handles posture-layer controls: managing configuration, governing identities and third-party access, and remediating risk inside the application. They're not redundant. They're complementary layers protecting different parts of the same environment.
That said, if your organization is choosing where to start, the calculus has shifted. The breaches making headlines today - OAuth-based data theft, misconfigured sharing settings, compromised third-party integrations, departing employees exfiltrating data - are SSPM problems, not CASB problems. The SaaS attack surface has moved inward, and your security tooling needs to follow.
The pattern that is seen among mature security teams? SSPM is used as the posture control plane for the SaaS environment, with CASB handling traffic enforcement where it's still needed (if it is at all).
Sure, here's a standalone section you can drop in:
Where DoControl Lands
DoControl is built as a pure SSPM platform - API-native, posture-first, and designed specifically for the risks that live inside SaaS environments rather than at their edges.
Where CASB tools inspect traffic, DoControl connects directly to the apps where your data actually lives - Google Workspace, Slack, Microsoft 365, Salesforce, GitHub, Box, and more - and examines what's happening inside them. Permissions, third-party integrations, shared files, AI agent access, configurations, and identity-level risk are all monitored continuously, not just at the moment of access.
The differentiator that matters most: DoControl doesn't stop at detection. Every risk it surfaces - a misconfigured sharing setting, a risky OAuth grant, an overprivileged contractor account - can be remediated automatically, through policy-driven remediation workflows that close the loop without requiring manual intervention.
Security teams define what they want their rules to be; DoControl enforces them at scale.
DoControl also brings identity and behavioral context to every alert, pulling signals from IdP and HRIS systems to distinguish a real threat from normal business activity. That context is what separates meaningful risk prioritization from alert fatigue.
For organizations that have relied on CASB for SaaS security, DoControl doesn't replace it wholesale - it fills the posture gap that CASB was never designed to address.
For organizations starting fresh, it's built for the threat environment that actually exists in 2026: identity-based attacks, OAuth-connected supply chain risk, AI agent sprawl, and configuration drift - all of it remediated, not just reported on.
The Bottom Line
CASB and SSPM are solving related but distinct problems. CASB watches traffic. SSPM watches posture. In the current threat environment - where the most impactful breaches are happening inside SaaS apps, not at the perimeter - SSPM has become the foundational layer for any serious SaaS security program.
The question isn't really SSPM vs. CASB. It's whether your security stack has visibility into what's actually happening inside your SaaS environment - and, more importantly, whether it can do something about it.
{{cta-1}}



