
Picture this: a senior engineer submits their resignation on a Friday afternoon. By Monday morning, they've downloaded 400 files from Google Drive, forwarded three Salesforce reports to a personal Gmail, and connected a new AI OAuth app to your Google Workspace environment.
Your legacy DLP tool? It flagged none of it. Every action looked like normal business activity, because technically, it was. The user had legitimate access. There was no malware. No suspicious IP. Just a person walking out the door with your data.
This is the reality of insider risk in a SaaS-first world. Sensitive data now lives across dozens of applications, and the people with access to it aren't always acting in your organization's best interest.
95% of cybersecurity incidents occur due to human error, and 83% of organizations have experienced an insider attack in the past year.
Behavioral analytics in SaaS security gives security teams the visibility and context they need to detect real threats, score risk intelligently, and act before hackers start moving laterally - and talking data out the door.
Why Traditional Security Tools Are Failing in a SaaS-First World
Imagine trying to catch shoplifters in a store with no cameras, only a list of banned items at the door. That's roughly what legacy DLP looks like in a modern SaaS environment that requires a context, AI-driven, purpose built SaaS DLP solution.
The legacy DLP tools were originally designed for perimeter-centric architectures, on-premises infrastructure, predictable network traffic, and static user populations. But, none of those conditions exist anymore. And, as new companies enter the fold and start scaling - they need a solution that actually protects the way data moves today.
Today's hacker groups don't exploit vulnerabilities. Security teams usually have these covered - or so they think. If you look at the most recent hacks (at least the ones this month), they are all insider-driven.
Today’s hackers simply log in. For example, the Vercel breach: ShinyHunters entered the environment through a Google Workspace OAuth app, used legitimate credentials, and then moved laterally through the environment - stealing data and then selling it on the dark web for millions.
Another example: the Kraken insider incident - where insiders with internal access allegedly stole data in an effort to extort the company for money.
And, the Mercor breach, where a hacker group claimed to have exfiltrated 4TB of data from Mercor’s systems via a third-party app.
Should we go on? These incidents were all insider related: someone with genuine, legitimate credentials was hacked or manipulated into giving access to sensitive data.
It's important to note that these three incidents happened all within the last two weeks. As AI driven attacks ramp up, the per-week number of attacks is only going to increase - and gaining access through legitimate user credentials remains the driving force and main point of entry.
The Verizon 2025 Data Breach Investigations report found that 22% of breaches start with compromised credentials, and 88% of basic web application attacks involve stolen credentials.
The bottom line? Modern attackers leverage legitimate credentials, trusted tools, and native system functions to operate silently within enterprise environments. These tactics and the escalation tactics are only more amplified with AI; AI-driven hacking tools are now enabling cyberattacks to move 4x faster than last year, with the fastest incidents reaching data exfiltration in just 72 minutes (Palo Alto Networks, 2026).
These attacks are deliberately designed to resemble normal business activity, which renders signature-based detection completely ineffective.
Legacy systems weren't built to understand that a user accessing an OAuth application via legitimate credentials that is actually a member of ShinyHunters trying to exfiltrate data is categorically different from a well meaning employee accessing that app to help them take meeting notes. All it shows you is that there was a log in - but there is ZERO context or data that accounts for:
- Why that access happened
- Who was performing the action
- What they were using it for
- What happened after
After all, static, binary rules don't account for:
- User roles (who is this person at the company? An intern, manager, VP?)
- User context (what is this user's normal scope, responsibilities, and day-to-day access/sharing activity?)
- Peer group behavior (what are their peers and department doing? Are there similar projects and events happening among them?
- Environmental context that separates a routine action from a red flag (did someone just put in their two weeks and are sharing documents? Is someone based in NYC, USA all of a sudden accessing files from Munich, Germany? THIS context determines whether it’s normal business ops vs. an insider threat or compromised account)
…And they were never meant to!
The result is a painful paradox: organizations either tune their rules too aggressively and drown in false positives, which leads many teams to disable controls entirely, leaving sensitive data completely unprotected…OR…they tune conservatively and miss the threats that actually matter.
Neither outcome is acceptable - especially at the enterprise level - where the majority of teams have thousands of users, and the average organization uses over 125 SaaS applications per employee (Gartner, 2026).
The question isn't whether legacy tools are broken. They are. The question is what a better approach actually looks like.
What Are Behavioral Analytics in SaaS Security, and How Do They Work?
Behavioral analytics is the process of collecting and analyzing data about how users, applications, systems, and devices behave across your environment. Rather than matching activity against a list of known ‘bad’, predefined patterns, it asks a different question: does this activity deviate from what's normal for this person, in this context, at this time?
It is continuously learning, using what is known as the ‘baseline’ and then juxtaposing it against anything that looks anomalous.
For example, a marketing manager continuously accesses and views Drive files in the folder called ‘Q2 Marketing Creatives’ or ‘2026 Social Media Strategy’. One day, that same marketing manager is logged as accessing, viewing, and sharing files from a ‘Product Roadmap 2026’ folder, or seen accessing and downloading development repositories.
THIS context immediately sets off alerts, and ideally - automated remediation workflows - as it clearly conveys that this behavior is not the norm of this user's role, scope, or day-to-day responsibilities.
Building a Baseline of "Normal"
The foundation of behavioral analytics is continuous data collection. Before you can detect anomalies, you need a deep, granular record of what normal looks like, not just for your organization broadly, but for each individual user, role, and peer group within it.
The more context your platform collects, the smarter your detection becomes over time. This is not a one-time snapshot. It's a living model that improves with every event logged. In most SaaS security tools and platforms today, this is all AI-driven. But, more ‘traditionally’, four key components work together to build and maintain that baseline:
User Behavior Analytics (UBA) monitors employee actions: logins, file access patterns, data transfers, sharing behavior, and session timing. It knows that a specific user typically accesses 20 to 30 files per day and almost never shares externally.
Entity Behavior Analytics (EBA) extends that monitoring beyond people to devices, applications, and connected third-party apps. If an OAuth application that's been dormant for six months suddenly starts accessing sensitive files, that's a signal worth investigating.
Machine learning (ML) models do the pattern recognition at scale that human analysts simply cannot. They surface subtle anomalies across millions of events, flagging the combinations that matter rather than individual data points in isolation. Critically, these models get sharper the more data they ingest. Richer data collection means fewer false positives and more confident detections over time.
Risk scoring ties it all together by assigning dynamic risk levels to behaviors, so your team can prioritize what actually needs attention rather than chasing every alert.
What Behavioral Signals Actually Look Like
Let's make this concrete:
- A user downloading 3x their normal file volume in a single day = data point.
This is still anomalous, the SaaS DLP or SSPM will flag and alert (or remediate) it, and it WILL be investigated, but it’s a single action.
- That same user doing it the week after submitting a resignation, after hours, while also sending a shared link to a Google Drive file containing PII to a personal Gmail account = pattern, with all of these events being evaluated in context and in relation to one another.
Behavioral analytics connect those dots in real time, but only because the platform has been collecting enough context to recognize that each individual action is out of character.
Other signals include: a third-party OAuth app suddenly accessing file types it never touched before; a user accessing sensitive records outside their normal working hours from an unfamiliar location; or a team member whose peer group accesses an average of 15 files per week suddenly accessing 300.
The numbers back up the approach. Behavioral analytics reduces mean time to detection from 81 days to 18 days (Ponemon Institute 2025). And 62% of organizations now favor user behavior-based tools for insider threat detection.
One honest caveat? Behavioral analytics alone, without data context, produces an incomplete picture.
Knowing that a user accessed 400 files is only meaningful if you also know those files contained regulated financial data or customer PII. Data classification and access context MUST be layered in.
Behavioral signals without sensitivity context can still leave you chasing the wrong risks. That is why organizations need a contextualized, AI-driven SaaS DLP that will show you the entire picture.
That's why the real operational value of behavioral analytics isn't just in what it detects. It's in how it arms your security team with enough context to stop chasing noise and start acting on the risks that actually matter. That's where risk scoring becomes the critical bridge between raw signal and informed action.
Risk Scoring in SaaS Security: From Alert Fatigue to Actionable Prioritization
Every security team knows the feeling: you open your dashboard to 200 alerts, spend four hours triaging, and find three that were actually worth investigating. Alert fatigue isn't just an inconvenience. It's a security failure mode. When analysts are overwhelmed, real threats slip through.
Behavioral analytics paired with dynamic risk scoring changes the equation entirely, but only when the scoring model has enough context to make meaningful distinctions.
How Risk Scoring Works, and Why Context Is Everything
Risk scoring aggregates behavioral signals, data sensitivity, access context, and user history into a composite score. The key word is composite. A user accessing a sensitive file isn't inherently risky.
Now, that same user accessing 400 files, sharing externally, submitting a resignation letter, and doing it all at 11pm on a Sunday, is a different story. Risk scoring surfaces the combination of signals, not just individual events.
But here's what makes the difference between a risk score that's useful and one that's just noise: context about the user. Without knowing a user's role, their typical access patterns, their peer group's behavior, and the sensitivity of the data they normally touch, a risk score is essentially a guess.
A finance analyst pulling a revenue report looks very different from an engineer in a completely unrelated department doing the same thing. The action is identical. The risk is not.
This is precisely why data collection is so foundational to effective risk scoring. The richer your platform's understanding of each user, the more accurately it can distinguish between a routine action and a genuine threat. A system that has only seen 30 days of user behavior will produce far noisier scores than one with six months of baseline data across roles, teams, and access patterns. Depth of data directly translates to quality of decisions.
Behavioral analytics is what makes that depth possible. Without it, security teams are forced to make risk decisions based on static attributes: job title, department, access level. Those attributes tell you almost nothing about intent or anomaly.
Behavioral analytics fills that gap by continuously answering the question: is this person acting like themselves right now? When the answer is no, and the data being touched is sensitive, that's when a high-confidence risk score earns its weight.
The same action carries different risk weight depending on who is performing it, what data is involved, and whether it deviates from peer group behavior. Risk scoring that accounts for all of these dimensions lifts the manual burden off security teams by surfacing the signal that genuinely warrants human attention, rather than forcing analysts to make those judgment calls on 200 undifferentiated alerts.
The organizational impact is measurable. Companies with insider risk programs pre-empted 65% of data breaches (Ponemon 2025). And 89% of Fortune 500 companies plan to implement behavioral risk analytics by 2026 (Gartner). This isn't a niche capability anymore. It's becoming the norm for companies who take their cybersecurity program seriously.
How DoControl Turns Behavioral Analytics Into Real-Time Protection
Behavioral analytics is only as valuable as what you do with it. Detection without action is just observation. Context without enforcement is just information. The real differentiator is what happens after risk is identified.
This is where DoControl operates differently.
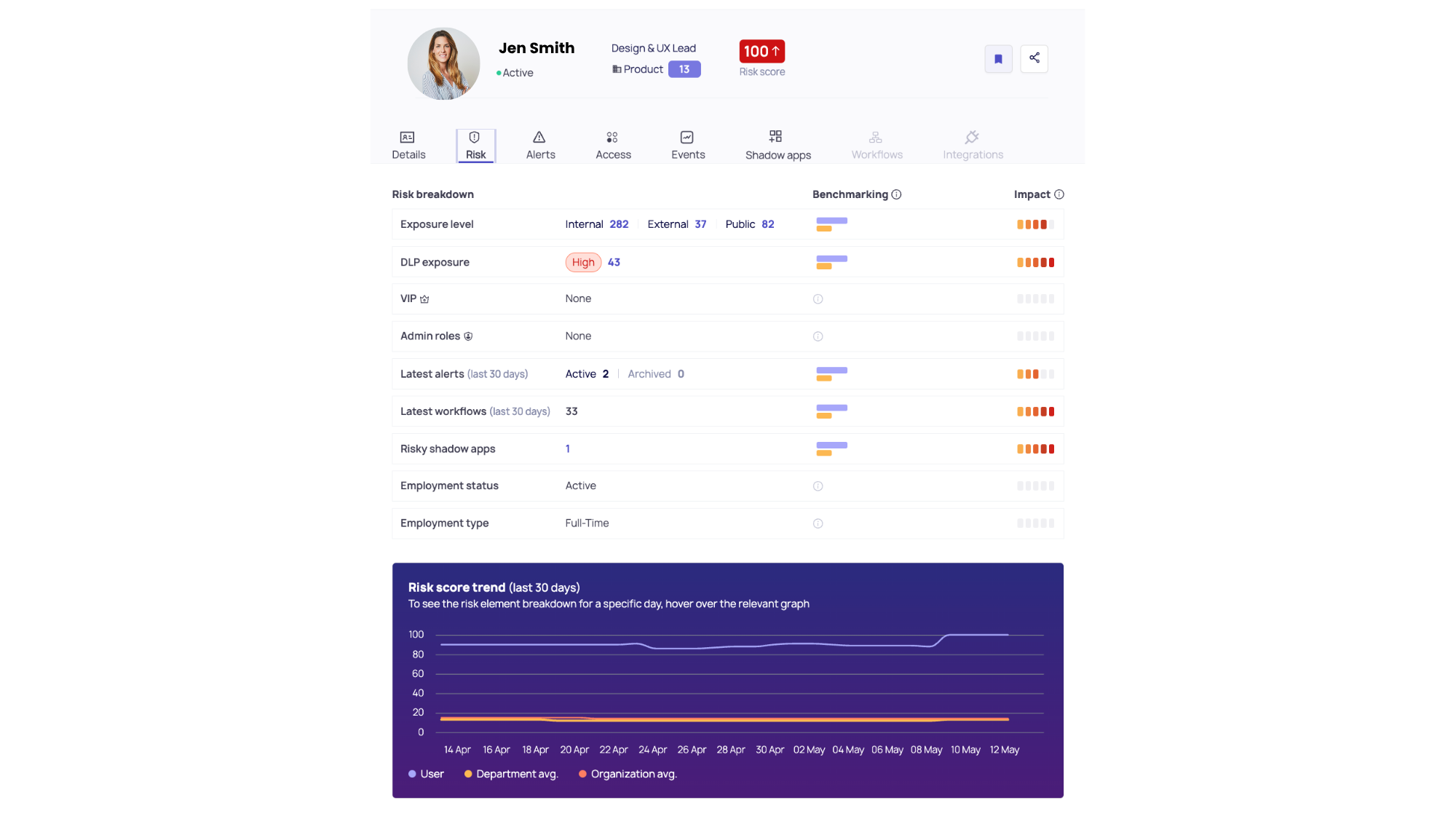
DoControl doesn’t just surface anomalous behavior. It connects behavioral signals, identity context, and data sensitivity into a single, continuous control loop that moves from detection to remediation in real time. Each user has a dynamic risk score that fluctuates and is continuously learning over time.
At the foundation, DoControl continuously builds behavioral baselines across users, applications, and connected third-party integrations.
It understands not just what actions are taking place, but who is performing them, what data is involved, and how those actions compare to historical patterns and peer group norms.
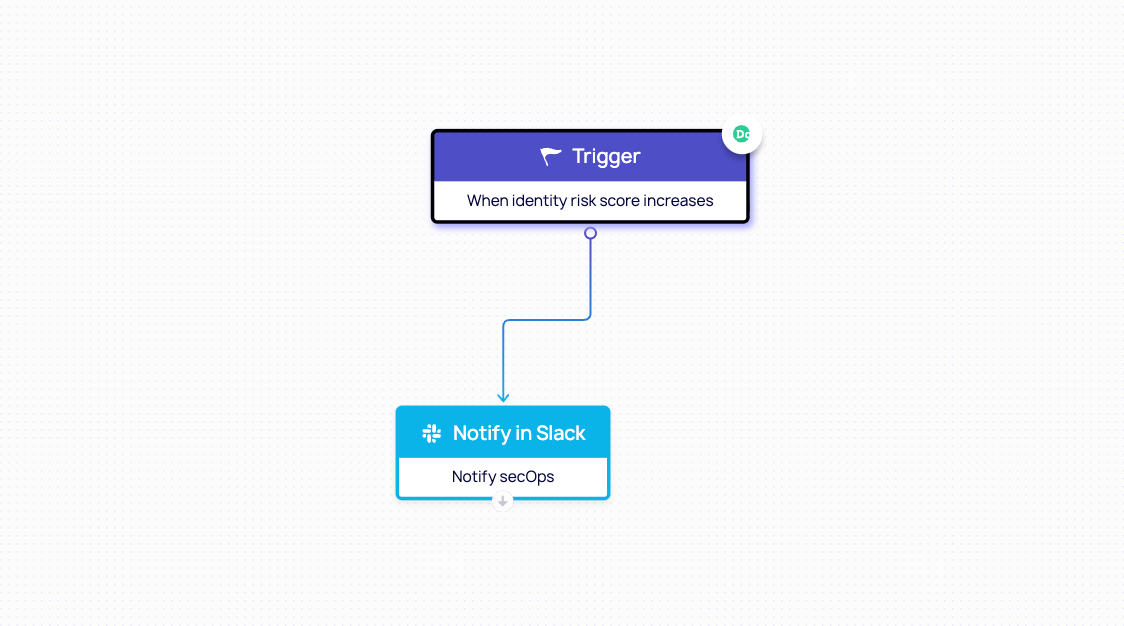
This allows the platform to distinguish between routine activity and true risk with a high degree of precision. Then, security teams can set up automated workflows to either notify SecOps about a spike in risk score, notify managers, or remediate any risks happening in real time. Here’s an example:
But the real power comes from layering this behavioral intelligence with deep data context.
DoControl maps where sensitive data lives across SaaS environments, classifies it based on risk (PII, financial data, intellectual property), and continuously monitors how that data is accessed, shared, and exposed. So when behavioral anomalies occur, they are immediately evaluated against the sensitivity of the data involved.
A user downloading files is one thing. A user downloading hundreds of files containing regulated customer data, after submitting a resignation, and sharing them externally? That’s a high-confidence risk event.
Instead of generating another alert, DoControl assigns a dynamic risk score that reflects the full context of the behavior: identity, intent signals, data sensitivity, and environmental factors. This allows security teams to prioritize instantly, without manual triage.
And critically, DoControl closes the loop with automated remediation.
When risk crosses a defined threshold, the platform can take immediate action: revoke external sharing links, quarantine sensitive files, disable risky OAuth applications, or suspend user sessions. These actions are not static rules. They are context-aware responses triggered by real-time behavioral risk.
This is what modern SaaS security requires: not just visibility into what happened, but the ability to understand why it happened, assess how dangerous it is, and stop it before data leaves the organization.
Because in today’s threat landscape, the difference between a normal user action and a security incident isn’t the action itself, it’s the context around it - and how quickly you can act on it.
Conclusion: From Visibility to Control in a SaaS-First World
The reality is simple: the way data moves has fundamentally changed, but for many organizations, security hasn’t kept up.
Data no longer sits behind a perimeter. It lives across dozens - sometimes hundreds - of SaaS applications, accessed by employees, contractors, and third-party integrations from anywhere in the world.
Security teams don’t need more alerts. They need clarity. They need prioritization. And most importantly, they need the ability to act - immediately and confidently - when risk is detected.
That’s the evolution from visibility to control. Platforms like DoControl represent that next step. By combining behavioral analytics with data classification, identity context, and automated remediation, they enable organizations to not only detect insider threats and compromised accounts, but to stop them before sensitive data is exposed.
Because in a SaaS-first world, the question is no longer whether your users have access to sensitive data. It’s whether you have the context and control to ensure that access isn’t abused.
Frequently Asked Questions (FAQ)
What is behavioral analytics in cybersecurity?
Behavioral analytics in cybersecurity is the process of collecting and analyzing data on how users, applications, and devices behave across an environment. It establishes a baseline of normal activity and continuously monitors for deviations such as unusual file access, atypical sharing patterns, or off-hours logins that may indicate an insider threat, compromised account, or data exfiltration attempt.
How does risk scoring work in SaaS security?
Risk scoring in SaaS security aggregates multiple behavioral signals including volume of files accessed, sensitivity of data involved, sharing destinations, time of activity, and deviation from peer group norms into a composite risk score. This allows security teams to move away from investigating every alert and instead focus on the highest-risk users and events.
How does behavioral analytics help with access controls?
Behavioral analytics enhances access controls by providing context that static permissions cannot. Even if a user has legitimate access to a file or folder, behavioral analytics can flag when that access is anomalous based on wrong time, wrong volume, or wrong destination. This gives security teams the ability to enforce access controls dynamically, tighten permissions based on risk signals, and investigate or remediate before data leaves the organization.
Can behavioral analytics detect insider threats before data is exfiltrated?
Yes, and this is one of its most important capabilities. By monitoring for pre-exfiltration signals like bulk downloads, external sharing spikes, and access to sensitive data outside normal patterns, behavioral analytics can surface insider threat risk before data actually leaves organizational control.



