With the rise of vibe coding and AI tools, more and more unsecured API keys are being generated every day to power the new applications being made.
The post below shows what can happen when such a key becomes truly compromised. It's the ultimate modern cybersecurity nightmare:
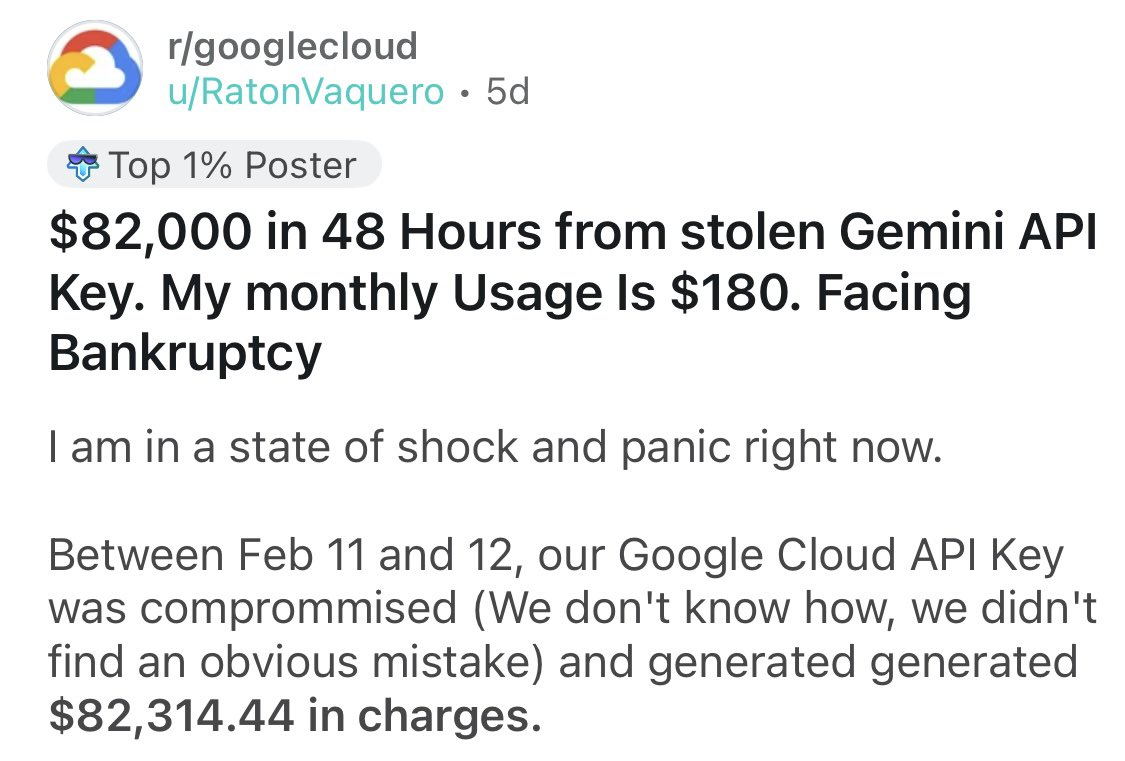
This isn't a hypothetical exercise. It's the devastating story of an active Reddit user after a simple API key for their Google Cloud environment was compromised. The key, which connects to the Gemini AI model, was used to generate over $82,314.44 in charges in just two days.
Why This is the Ultimate Modern Threat
This story is a masterclass in the failures of the traditional security mindset. Let’s dissect the problem:
1) The Mystery of the Breach: The user explicitly states, “We don't know how, we didn't find an obvious mistake.” This means a simple misconfiguration or public GitHub repo check didn't reveal the leak. The theft was subtle. Was there an admin setting in GCP that could have capped the charges far below $82,000? The user was unaware because misconfigurations were not being tracked at scale.
2) Velocity of the Harm: Traditional security models often rely on polling or batch processing (checking posture once a day). An attacker doesn't need a day. In this case, they didn't even need a weekend. They generated a life-altering financial loss in just 48 hours. AI tools make it easier to rack up charges due to pricing differences (tokens vs. compute). This is why users need security that is always on, and happening in real-time - not a periodic scan.
3) The Identity Crisis: A stolen API key is a stolen Non-Human Identity (NHI). Traditional endpoint security tools and Identity Providers (IdPs) are terrible at managing these, and yet they are the most powerful credentials in a modern SaaS stack. A single API key is a master key to your AI models, data storage, and critical applications. It’s crucial that they are monitored, governed, and secured effectively.
Traditional Tools Are Too Slow and Too Blind
This is where traditional SaaS Security Posture Management (SSPM) tools fail. They are static. They are designed to tell you about your configuration after the bill arrives. They'll show you a dashboard on Monday morning that says your budget was exceeded... right after you’ve already been billed $82,000.
Visibility is a commodity. If your strategy stops at simply 'seeing' the key, you’ve already lost. The problem isn't that a key could be stolen; it’s that it was stolen, and was allowed to perform an unauthorized action (generating a massive amount of data/cost) for 48 hours with zero intervention.
The most dangerous "insider threat" in 2026 isn't a human. It's a non-human identity with a credit card. A monthly bill for an annual mistake is not a viable business model. You cannot afford to operate your security on a polling basis when your attackers are operating on an event basis.
Security events NEED to lead to consequential outcomes. Breaches like this need to have actions attached to them, preferably automated. Was the key compromised? Don’t just notify one party, notify the whole team! Give the full context: when did this happen, what platform, what's the unique ID of the key? Metadata is essential for understanding the context on what the details of the breach are.
Conclusion
This Reddit thread is more than just a cautionary tale; it’s a symptom of a shifting landscape where the speed of innovation has outpaced the speed of traditional oversight.
When a single API key can generate a life-altering bill in a single weekend, "checking the logs" manually is no longer a viable defense.
The real takeaway here isn't just about better password hygiene - it’s about building automated guardrails and overarching posture management that can step in when things go sideways in real-time.
Whether you’re a startup or an enterprise, the goal is still the same: ensuring that a 48-hour anomaly remains a minor alert rather than a business-ending event.



