.png)
Organizations today operate in the cloud and run on SaaS. Collaboration platforms, CRM systems, productivity suites, and AI-powered tools are now deeply embedded in daily workflows. These tools make work faster and more connected - but they also introduce a new challenge: controlling how sensitive data is accessed, shared, and exposed across an increasingly complex ecosystem.
That’s where data governance comes in.
Data governance has evolved far beyond traditional compliance frameworks that exist to check boxes. Today, it must address dynamic SaaS environments, automated integrations, external collaborators, and even AI agents interacting directly with business data.
In this article, we’ll explore:
- What data governance means today
- Why it has become critical in modern SaaS environments
- Emerging trends shaping the future of data governance
- How DoControl approaches data access governance and helps organizations secure SaaS data at scale
What Is Data Governance?
At its core, data governance is the framework organizations use to manage how data is accessed, shared, protected, and controlled.
It defines:
- Who is accessing data
- What data they're accessing
- Why they're accessing it
- Is that access within scope or is it risky
- Is that data being moved
- Are non human identities accessing data
And more.
Within SaaS environments, this becomes data access governance, which focuses specifically on controlling and monitoring access to sensitive assets across cloud and SaaS applications.
A modern governance strategy typically includes:
- Access policies and permissions management
- Data classification and sensitivity controls
- Monitoring and auditing of access activity
- Compliance enforcement
- Automated remediation when policies are violated
In other words, data governance ensures that the right people have access to the right data - and no one else does.
Why Data Governance Is More Critical Than Ever
The need for robust governance has increased dramatically over the past decade. Several forces are driving this shift.
1. SaaS Sprawl
Organizations now rely on dozens or even hundreds of SaaS applications. These platforms store massive volumes of business data and often integrate with each other, making it difficult to maintain visibility over where sensitive information lives or how it’s being shared.
Each application has its own permission structures, sharing settings, and APIs, which creates fragmented access policies and inconsistent security controls.
Without centralized governance, sensitive assets can easily become exposed and SaaS sprawl multiplies.
2. The Ease of Data Sharing
One of the biggest advantages of SaaS platforms is how easy they make collaboration. Employees can share files internally, externally, or publicly with just a few clicks.
But this convenience comes with risk.
Overexposed files, outdated permissions, and forgotten sharing links accumulate quickly, creating a large attack surface that can lead to data leaks or breaches.
Employees often share files without security in mind, as their main priority is getting their tasks done as quickly as possible. This is where the gap begins.
3. Identity-Driven Access
In SaaS environments, identity is the primary access control mechanism.
Employees, contractors, third-party collaborators, integrations, nonhuman identities (AI agents, service accounts, bots, etc.), ALL access data through an identity.
If those identities are compromised, misconfigured, or overly privileged, insiders or external attackers gain access to the same data those identities can reach.
This makes identity governance a foundational component of modern data governance.
Emerging Trends in Data Governance
As the SaaS ecosystem evolves, data governance is also undergoing a transformation. Several trends are shaping the next generation of governance strategies.
The Rise of Non-Human Identities
Not all identities accessing SaaS platforms belong to employees.
Modern environments include non-human identities (NHI’s) that manifest themselves as:
- AI agents
- OAuth applications
- Automation scripts
- API tokens
- Third-party integrations
- Bots and system accounts
These non-human identities often have broad permissions and persistent access to data.
Without visibility and governance, they can quietly become one of the largest security risks in an organization.
AI Agents and Autonomous Systems
AI tools and agents are rapidly being integrated into enterprise workflows. These systems increasingly interact with SaaS platforms directly, reading, processing, generating data...the list goes on. Examples include:
- AI copilots (Gemini, Copilot, Glean) accessing + analyzing documents
- Generative AI tools accessing internal knowledge bases
- AI agents executing workflows across multiple SaaS apps
While powerful, these systems introduce a new governance challenge: AI entities accessing sensitive data at scale.
When AI systems interact with organizational SaaS data, companies often have little visibility into what those systems are doing with it. If an AI agent downloads data into a workspace, an account becomes compromised, or sensitive information is exported outside the environment, organizations can quickly lose control of their data and expose themselves to significant risk.
Data shows that the majority of the actions taken in SaaS environments today are actually performed by non-human identities. Based on an analysis of activity logs across enterprise environments, DoControl found that:
- In Microsoft SharePoint, it was analyzed that approximately 70% of all actions were taken by non-human identities rather than by human users.
- In Microsoft OneDrive, it was analyzed that around 60% of all recorded activity was generated by non-human identities acting on behalf of users.
- In Slack Enterprise environments, it was analyzed that approximately 53% of all data access events were performed by non-human identities, primarily through enterprise search queries and file indexing.
- In Box environments, it was analyzed that nearly 45% of all observed activity was generated by non-human identities instead of human users.
- In Salesforce environments, it was analyzed that around 45% of recorded events were driven by non-human identities operating within the platform.
- In Google Drive environments, it was analyzed that approximately 40% of all actions were performed by non-human identities rather than by human users.
These non-human identities (NHIs) have the ability to view, share, download, export, or even exfiltrate any data they come into contact with. And, in many cases, they operate using the credentials or identity of a legitimate employee within the organization. This is why context is SO important, which we’ll get into in the next section.
As a result of this emerging trend, organizations must ensure that AI systems and other non-human identities only access appropriate files, and that all interactions with sensitive data are properly logged, monitored, controlled, and remediated in real time.
Context-Enriched Governance
Following our last trend, context-enriched governance is the only way to actually understand, control, and implement flexible security controls that don't slow down the business in 2026.
Traditional access models relied on static roles and permissions. However, modern governance is moving toward contextual access control, which evaluates additional signals such as:
- User identity and role
- Behavioral patterns
- Location and device
- Access history
- Time of access
- Data sensitivity
This contextual approach allows organizations to apply policies dynamically and enforce governance without disrupting legitimate business workflows.
Why Context Is the Key to Effective Data Governance
An action alone is simply an action. It’s the context surrounding that action that determines whether it is normal business activity or a potential security risk.
For example, imagine a Senior Vice President of Finance mass-sharing highly confidential financial documents with an external domain. On its own, that action might appear risky. But if it happens during tax season and the files are being shared with an approved external accounting firm, the behavior is completely legitimate and necessary to keep the business running.
Now consider the same action under different circumstances. The same SVP of Finance has recently submitted their two-weeks notice, is preparing to join a competitor, and begins sharing sensitive documents to an external domain (that happens to be a personal email account). In this case, the context surrounding the action dramatically changes its risk profile.
This is where modern SaaS data governance solutions must go beyond static access controls.
By incorporating contextual signals - such as employment status, department changes, historical baseline behavior, external sharing destinations - security teams can determine whether an action is normal or requires intervention. The goal is not to block collaboration, but to identify truly risky activity and respond accordingly.
To achieve this level of visibility, governance platforms must integrate with systems that provide identity and organizational context, such as:
- HRIS systems, which provide employment status, role changes, and department movements
- Identity providers (IdPs), which supply authentication data, identity risk signals, and access privileges
Together, these signals help security teams understand who is accessing data, why they are accessing it, and whether the behavior aligns with normal business operations.
Why Context Matters Even More in the Age of AI Agents
As we mentioned above, context becomes even more critical as AI agents and non-human identities enter SaaS environments.
For instance, imagine an AI agent integrated into a company’s Google Workspace environment that assumes the identity of a Senior Product Manager, let’s call her Anna. If that identity (acting as Anna) is accessing product documentation and feature roadmaps from their usual location in New York, USA, the activity likely appears normal and consistent with the role.
But if that same identity (Anna - but really an AI agent that has assumed her credentials), suddenly begins downloading large volumes of files from Switzerland and accessing sensitive sales pipeline data instead of product documentation, the context changes significantly.
The action itself - accessing files - may not be inherently suspicious. But the who, what, where, and when surrounding the activity signal that something may be wrong.
This contextual understanding is what allows security teams to determine whether behavior falls within the bounds of legitimate business activity, or represents a potential threat.
How Context-Driven Governance Enables Smarter Security Decisions
Contextual intelligence enables organizations to move beyond rigid, one-size-fits-all security rules.
Instead of blocking actions outright, security teams can:
- Identify anomalous behavior
- Trigger automated remediation workflows
- Alert security teams when risk thresholds are crossed
- Apply policy enforcement only when necessary
This approach allows organizations to protect sensitive data without disrupting the collaboration that SaaS platforms are designed to enable.
How DoControl Solves for SaaS Data Governance
DoControl was built to address one of the most pressing security challenges facing modern enterprises: governing SaaS data access at scale without slowing down collaboration.
Our platform focuses on reducing SaaS data exposure through visibility, policy enforcement, and automated remediation.
Organizations use DoControl to discover data assets, understand exposure risks, and enforce access governance across their SaaS environments.
Visibility without control is useless. Many solutions promise protection, but they stop at visibility, alerts, and dashboards.
Unlike these solutions claiming control, DoControl actually delivers it. DoControl goes further - delivering not only the visibility organizations need, but also the remediation capabilities and control required to truly secure and govern SaaS environments.
DoControl approaches data governance through several core capabilities.
1. SaaS Data Discovery and Asset Inventory
You can’t protect what you can’t see.
DoControl automatically builds an inventory of all assets across your most meaningful, connected SaaS platforms, identifying:
- Files and documents
- Shared drives
- Users and collaborators
- Groups
- OAuth applications
- Metadata and activity events
This discovery layer eliminates blind spots and provides security teams with a centralized view of their SaaS data landscape.
2. Exposure Mapping and Risk Prioritization
Once data assets are discovered, DoControl evaluates their exposure level and sensitivity.
The platform assigns risk and sensitivity scores based on:
- Sharing configuration
- Public or external exposure
- Identity risk signals
- Behavioral activity
This allows security teams to prioritize remediation efforts and focus on the most critical exposures first.
3. Context-Aware Data Access Controls
One of DoControl’s key differentiators is its use of contextual signals to enforce governance policies.
Rather than applying rigid blanket rules, policies can incorporate contextual information such as:
- User roles and departments
- Admin privileges
- Historical behavior
- Access patterns
- Identity risk scores
This approach allows organizations to maintain strong governance while minimizing friction for legitimate collaboration.
4. Identity-Driven Governance
As we’ve touched on, data governance in SaaS is inseparable from identity governance.
DoControl’s identity capabilities provide visibility into:
- Human identities (employees, contractors, vendors)
- Non-human identities (AI agents, OAuth apps, service accounts)
- Access privileges across SaaS applications
By combining identity insights with data exposure monitoring, organizations can better understand who is accessing what data - and why.
5. Automated Remediation at Scale via Workflows
Visibility alone is not enough, true data governance requires action.
DoControl equips its users with robust remediation capabilities. Remediation can be performed in two primary ways:
1. In bulk, en masse
When organizations first onboard with DoControl, there is always a large backlog of historical exposures that need to be addressed. These exposures - such as overshared files, outdated permissions, or risky sharing settings - are identified during a Free Risk Assessment or Proof of Value (POV).
{{cta-1}}
From there, customers can remediate large volumes of assets in bulk, allowing them to quickly clean up their SaaS environment.
2. Automated workflows that run 24/7
Once the initial cleanup is complete, organizations can set up automated workflows to continuously monitor and remediate risks. DoControl offers pre-built, out-of-the-box playbooks for many common scenarios, while also allowing customers to create custom workflows tailored to their specific policies and use cases.
Our team works very closely with customers to help design and deploy these workflows so they can get the maximum usage out of our platform.
These automated workflows could be the following scenarios:
- Revoking public sharing links
- Removing unauthorized collaborators
- Expiring outdated file permissions
- Suspending sessions during anomalous activity
- Revoking high-risk OAuth integrations
- Time-boxing shares to certain employees or third parties
- Cutting off access if their is a suspicious action
- Engaging management of security teams after a certain trigger
…and the list goes on.
These automated workflows allow security teams to remediate risks across hundreds of thousands of assets in minutes rather than days.
For example, here’s an example of a simple workflow that revokes 3rd party sharing:
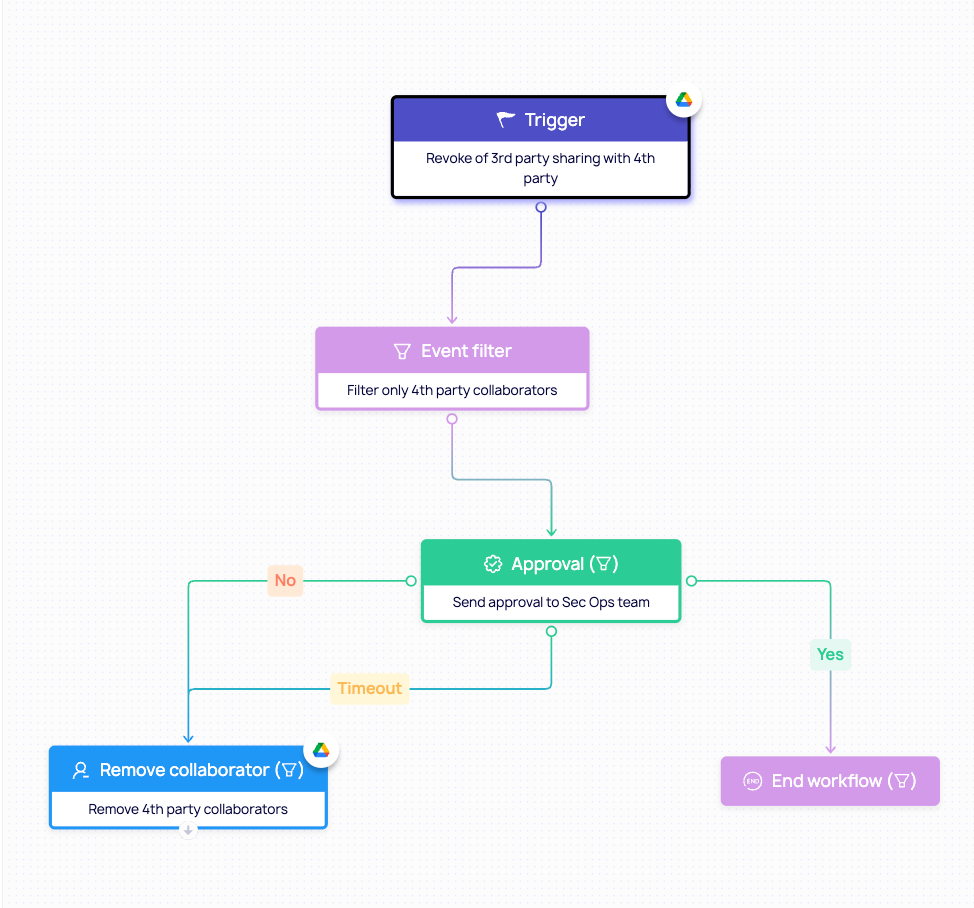
Workflows can also be customized to be more complex depending on a customer’s needs, risk profile, and the other existing tools or solutions in their security stack.
6. Leveraging Google Labels and Metadata
DoControl enhances governance by leveraging labels and signals from SaaS platforms such as Google Workspace.
This includes:
- Google Drive labels
- File metadata
- Ownership information
- Organizational roles
By integrating with these signals, DoControl allows policies to incorporate data classification and organizational context, improving governance precision.
Here’s an example of a customer workflow that leverages Google labels to classify data:
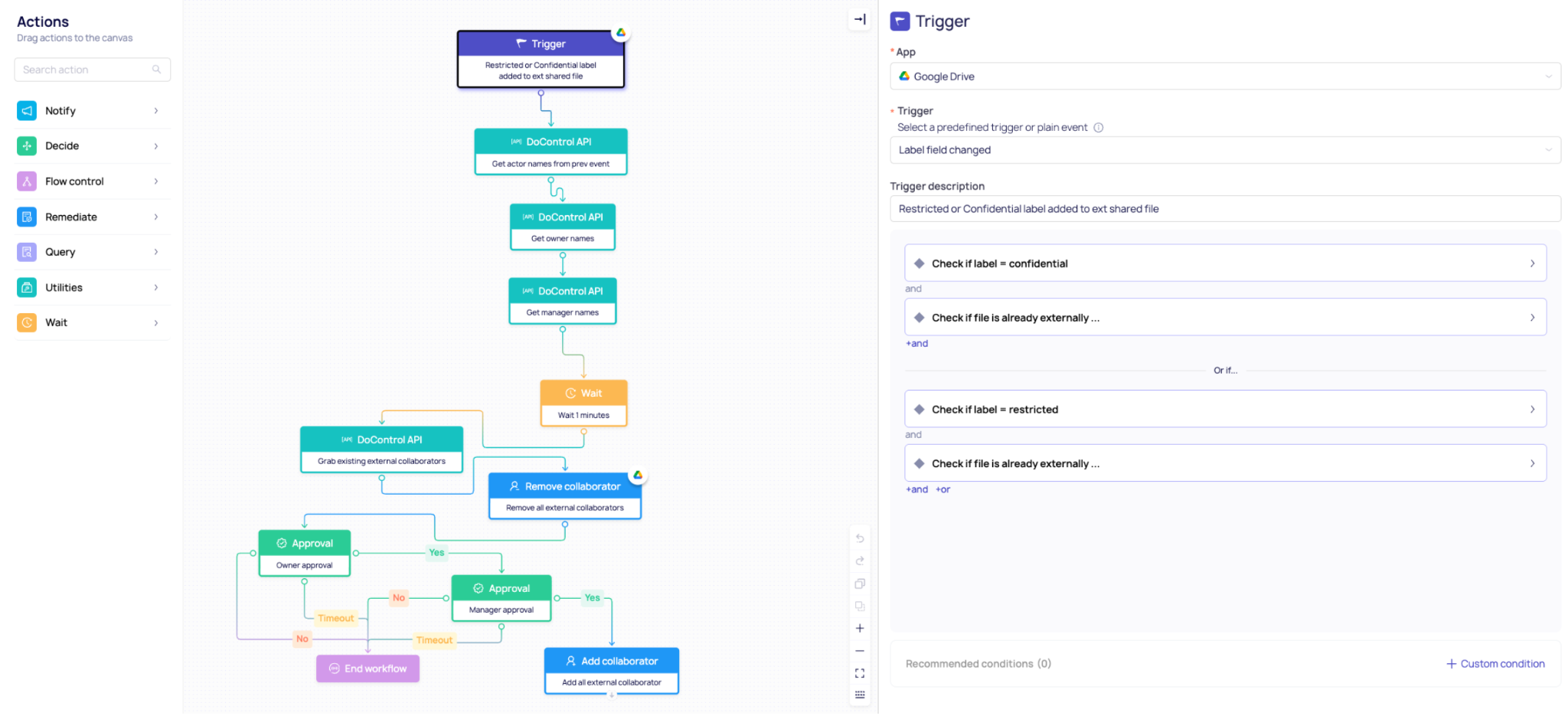
DoControl recognizes that different solutions address different security challenges. That’s why we integrate with existing tools to help customers achieve stronger, more comprehensive security.
The Future of SaaS Data Governance
As SaaS adoption continues to expand and AI systems become embedded into business workflows, the challenge of governing data access will only grow more complex.
Future-ready governance strategies must:
- Understand identity context
- Monitor real-time data exposure
- Support both human and non-human identities
- Scale across hundreds of SaaS applications
- Automate remediation and control
Data governance in 2026 needs to support all of the above bullets in order to truly protect the way data moves in SaaS today.
Final Thoughts
Data governance is no longer just a compliance exercise. It has become a core security discipline for organizations operating in SaaS-driven environments.
With employees, collaborators, integrations, and AI agents all interacting with company data, organizations need governance solutions that deliver:
- Visibility
- Context
- Automation
- Control
DoControl helps security teams achieve exactly that - enabling organizations to share freely while maintaining control over all of their SaaS data.



