
Misconfigurations don’t break all at once, they build up over time.
A Google Drive sharing policy is tightened ahead of an audit.
A few weeks later, an admin loosens a setting to unblock a request.
A new team connects a third-party app to move faster on a project.
Each decision makes sense in the moment, but over time, these small changes compound.
Months later, security teams find themselves dealing with the same exposure they thought they had already fixed - except now it’s spread across more applications, more users, and more data.
This is the reality of configuration drift: the gradual, continuous deviation from an organization’s intended security posture.
Most solutions attempt to surface these issues. They generate alerts, open tickets, and highlight misconfigurations. But they stop there. And while alerts sit in queues, the environment continues to drift. This is the core challenge security teams face today:
Misconfigurations aren’t a one-time problem, they’re a continuous one.
And in SaaS environments, these misconfigurations happen constantly.
They can stem from:
- Default settings that prioritize collaboration over security
- Users unknowingly oversharing sensitive data
- Third-party integrations with excessive permissions
- Changes in roles, teams, or projects that leave access outdated
- Lack of centralized visibility across applications
The challenge is that these risks often go unnoticed.
From a surface-level view, everything appears to be functioning as expected. But beneath that, sensitive data may already be exposed.
This creates a critical problem:
Organizations don’t just need to secure data, they need to continuously validate that their environments are configured correctly.
This is where misconfiguration management becomes essential.
At a high level, effective misconfiguration management enables organizations to:
- Identify risky or incorrect configurations across SaaS applications
- Understand how those configurations impact data exposure
- Detect misconfigurations in real time
- Remediate issues quickly and at scale
- Continuously enforce secure configurations without disrupting users
But, traditional approaches fall short. Many solutions rely on periodic scans, static policies, or manual audits - leaving gaps in visibility and delayed response times.
Modern organizations need a new approach: one that is continuous, context-aware, and built for dynamic SaaS environments.
What Is Misconfiguration Management?
At its core, misconfiguration management is the process of identifying, monitoring, and correcting incorrect or risky settings across systems that could lead to data exposure or security vulnerabilities.
In SaaS environments, this extends beyond infrastructure and into how data is shared, accessed, and controlled within applications.
It answers a critical question:
Are our systems and data configured in a way that protects us - or exposes us?
Misconfigurations in SaaS can take many forms, including:
- Public or overly permissive sharing settings
- Files shared with unintended external users
- Third-party applications with excessive access
- Misconfigured permissions across users or groups
- Data accessible beyond what is required for a role
A modern misconfiguration management strategy provides visibility into:
- Where misconfigurations exist
- What data is impacted
- Who has access as a result
- How those configurations were created
- Whether they introduce risk to the organization
But visibility alone is not enough. To be effective, misconfiguration management must also enable organizations to take action.
Within SaaS environments, a comprehensive approach typically includes:
- Configuration monitoring → Continuously tracking settings and changes across SaaS applications
- Exposure analysis → Understanding how misconfigurations impact data accessibility and risk
- Detection of risky configurations → Identifying public links, excessive permissions, and misaligned access controls
- Context-aware evaluation → Incorporating user roles, behavior, and business context to determine risk
- Real-time alerting and response → Detecting and responding to misconfigurations as they occur—not after the fact
- Automated remediation → Correcting risky settings, revoking access, and enforcing policies at scale
In short, modern misconfiguration management ensures that small configuration mistakes don’t turn into large-scale data exposure events.
Why Misconfiguration Management Is Critical Today
As SaaS adoption continues to grow, misconfigurations have become one of the leading causes of data exposure.
Sensitive data is constantly being shared, accessed, and updated across dozens of applications, each with its own settings, permissions, and controls. A single misconfiguration can expose that data instantly, often without anyone realizing it.
Several key factors are driving this risk:
1. SaaS Environments Are Highly Dynamic
SaaS environments are constantly changing.
Users join and leave teams, permissions are updated, files are reshared, and integrations are added or removed. With so many moving parts, configurations can quickly become outdated or misaligned with security policies.
2. Default Settings Favor Collaboration Over Security
Many SaaS platforms are designed to prioritize ease of use and collaboration.
Features like public sharing links, external access, and broad permissions are often enabled by default - making it easy for users to unintentionally expose sensitive data.
3. Lack of Visibility Across Applications
Organizations often lack centralized visibility into how configurations are set across their SaaS stack.
Without a clear view, misconfigurations - such as publicly exposed files or excessive permissions - can persist unnoticed for long periods of time.
4. Human Error Is Inevitable
95% of security incidents happen as a result of the humans at the company. Whether accidentally or on purpose, employees are the weakest link when it comes to keeping a secure SaaS environment.
That being said, most misconfigurations are not malicious, they are the result of simple mistakes. Employees may share a file with the wrong audience, grant too much access, or forget to revoke permissions after a project ends. Over time, these small errors accumulate into significant risk.
5. Third-Party and Integration Risk
Third-party applications and integrations often require access to data to function.
If these integrations are over-permissioned or misconfigured, they can introduce additional exposure paths - often outside of security teams’ visibility.
TLDR: Misconfigurations are difficult to detect, easy to overlook, and capable of causing significant damage.
Emerging Trends Shaping Misconfiguration Management
As SaaS environments evolve, so do the types of misconfigurations that put organizations at risk.
What was once limited to simple permission errors has now expanded into a much broader challenge - driven by AI adoption, identity sprawl, and increasingly complex sharing models.
Three key trends are reshaping how organizations must approach misconfiguration management today:
1. AI Applications and Misconfigured Data Controls
The rapid adoption of AI tools - such as ChatGPT and Claude - has introduced a new layer of AI configuration risk.
When employees connect these applications to SaaS environments, they often grant access to internal data without fully understanding how that data is being used.
Many of these tools:
- Ingest and process company data
- Store prompts and outputs
- May use data to improve or train models (depending on configuration)
If not properly configured, sensitive information can be unintentionally exposed or retained outside of the organization’s control.
Recent incidents - such as the Mercor data breach - demonstrate how the use of open-source and generative AI tools can introduce risk when settings are misconfigured. These cases highlight how easily sensitive data can be unintentionally exposed, reinforcing the importance of properly governing how AI applications access and interact with enterprise data.
As AI adoption accelerates, organizations must ensure that data access, retention, and sharing settings are properly configured from the start.
Identity and Agent-Based Configuration Risk
Today’s SaaS environments are no longer just user-driven - they are increasingly identity- and agent-driven.
Non-human identities (NHIs), service accounts, and AI agents are now interacting with systems and data at scale. These identities often require specific permissions and configurations to function - but if misconfigured, they can introduce significant risk.
For example:
- An AI agent may be granted broader access than necessary
- A service account may retain permissions long after it is needed
- An integration may be configured with excessive privileges across multiple systems
What makes this especially challenging is that these identities often operate silently in the background, without direct human oversight.
If their configurations are incorrect, they can continuously access, move, or expose data - without triggering traditional security alerts.
This makes it critical for organizations to not only manage human access, but also ensure that non-human identities are properly configured, monitored, and governed.
Over-Permissive Sharing and Public Exposure
One of the most common - and dangerous - misconfigurations in SaaS environments is over-permissive sharing.
Features like public links, external sharing, and broad access permissions are designed to enable collaboration. But when misconfigured, they can quickly expose sensitive data.
Recent high-profile incidents, such as the Scale AI data breach, have demonstrated how overly permissive sharing settings can lead to large-scale data exposure.
In that case, files configured with “anyone with the link” access exposed thousands of sensitive documents, including proprietary materials and confidential data.
These types of misconfigurations often persist because:
- Sharing settings are not continuously monitored
- Access is not revoked after projects end
- Users prioritize speed over security
As a result, sensitive data remains exposed long after it should have been secured.
The Shift Toward Continuous, Context-Aware Configuration Management
These trends point to a broader shift.
Misconfiguration management is no longer just about identifying incorrect settings - it’s about understanding how those settings interact with data, identities, and behavior in real time.
Organizations need solutions that can:
- Continuously monitor configurations
- Understand the context behind access and sharing
- Detect when configurations introduce real risk
- Automatically remediate issues before they lead to exposure
In today’s SaaS environments, a single misconfiguration is all it takes to create a breach.
How DoControl Solves Misconfiguration Management
DoControl was built to solve one of the most persistent and overlooked challenges in SaaS security:
Misconfigurations don’t happen once, they continuously drift OVER TIME.
Unlike traditional vulnerabilities, misconfigurations don’t fail loudly. They degrade silently.
A policy is tightened for an audit.
An admin temporarily relaxes a setting to unblock work.
A new integration is added to meet a deadline.
Weeks later, the same risk reappears - often in more places, across more users, and impacting more data.
This is configuration drift: the constant deviation from your intended security posture.
And in SaaS environments, drift isn't a one-time worst case scenario, it’s the default.
Why Traditional Approaches Fall Short
Most solutions on the market stop at detection.
They:
- Surface misconfigurations
- Generate alerts
- Create tickets
And then they stop. But drift doesn’t stop. Which means remediation can’t stop either.
DoControl’s Approach: From Detection to Continuous Enforcement
DoControl takes a fundamentally different approach.
We don’t just detect misconfigurations, we continuously enforce your desired security posture through an always-on, event-driven system.
At the core of this is what we call a closed-loop enforcement model:
Detect → Decide → Fix → Verify → Evidence
This is the difference between:
- Knowing you have misconfigurations
- And ensuring they don’t persist
DoControl approaches misconfiguration management through six core capabilities:
1. Continuous Posture Discovery and Baseline Establishment
You can’t manage misconfigurations without knowing what “secure” looks like.
DoControl evaluates your SaaS environment across hundreds of security controls and establishes a baseline posture aligned to best practices and frameworks.
This includes:
- Sharing and access configurations
- External collaboration settings
- OAuth and third-party app controls
- Admin and tenant-level configurations
This baseline becomes your source of truth - defining what is compliant vs. what has drifted.
2. Event-Driven Telemetry (APIs + Audit Logs)
Misconfigurations don’t always show up in configuration APIs.
Some of the most critical changes - like admin actions, OAuth grants, or group-level updates - are only visible through audit logs and event streams.
DoControl ingests telemetry from:
- SaaS APIs
- Audit logs
- Activity streams
This allows us to detect real configuration changes as they happen, not just periodic snapshots.
Because in SaaS, drift is often an event - not just a state.
3. Drift Detection with Context Enrichment
When a misconfiguration occurs, DoControl doesn’t just flag a setting change.
We provide full context:
- Who made the change
- What changed (before → after)
- What data or systems are impacted
- Why it matters from a risk and compliance perspective
For example:
A file becomes publicly accessible.
That alone is a signal.
But when enriched with context:
- It contains sensitive data
- It was shared externally
- It was changed by a user outside of policy
It becomes a clear, actionable risk.
4. Context-Aware Policy Enforcement
Not every configuration change should be treated the same.
DoControl applies policy logic with context, allowing organizations to:
- Automatically remediate high-confidence risks
- Route sensitive changes for approval
- Allow controlled exceptions when needed
This ensures that:
- Security is enforced consistently
- Business workflows are not disrupted
Because the goal isn’t to block changes - it’s to control them intelligently.
5. Automated Remediation Workflows at Scale
Detection without action is not misconfiguration management.
DoControl uses event-driven, no-code workflows to automatically remediate drift in real time.
These workflows include:
- Policy logic
- Conditional routing
- Approval steps
- Automated remediation actions
Examples of real-world workflows:
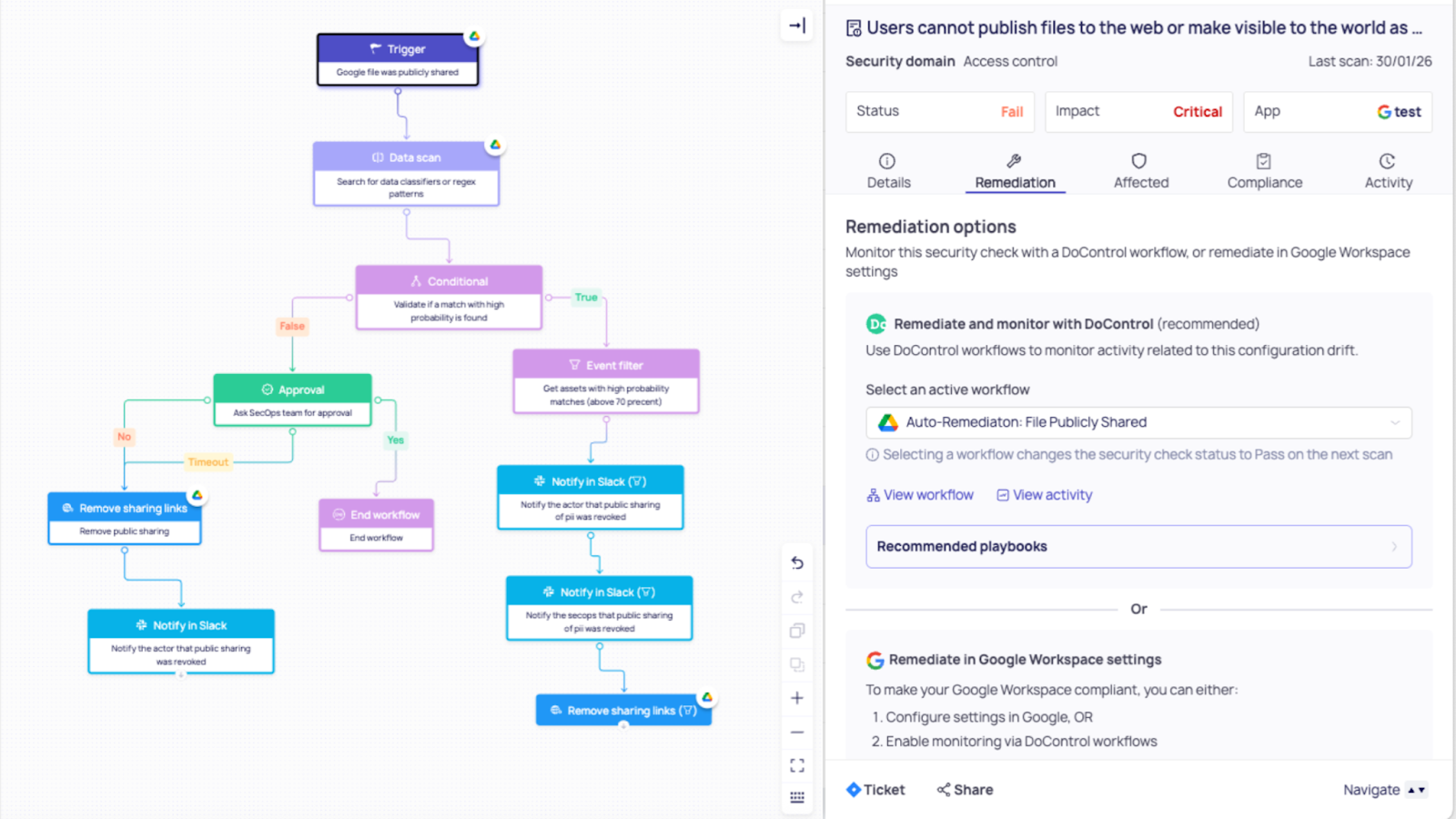
Example 1: Public File Sharing Exposure
A file becomes publicly accessible (“Anyone with the link”).
Workflow:
- Notify file owner and security with full context
- Check sensitivity level of the file
- If high-risk → require approval
- If not → automatically revoke public access
Outcome:
- Immediate exposure reduction
- No manual intervention
- Full audit trail
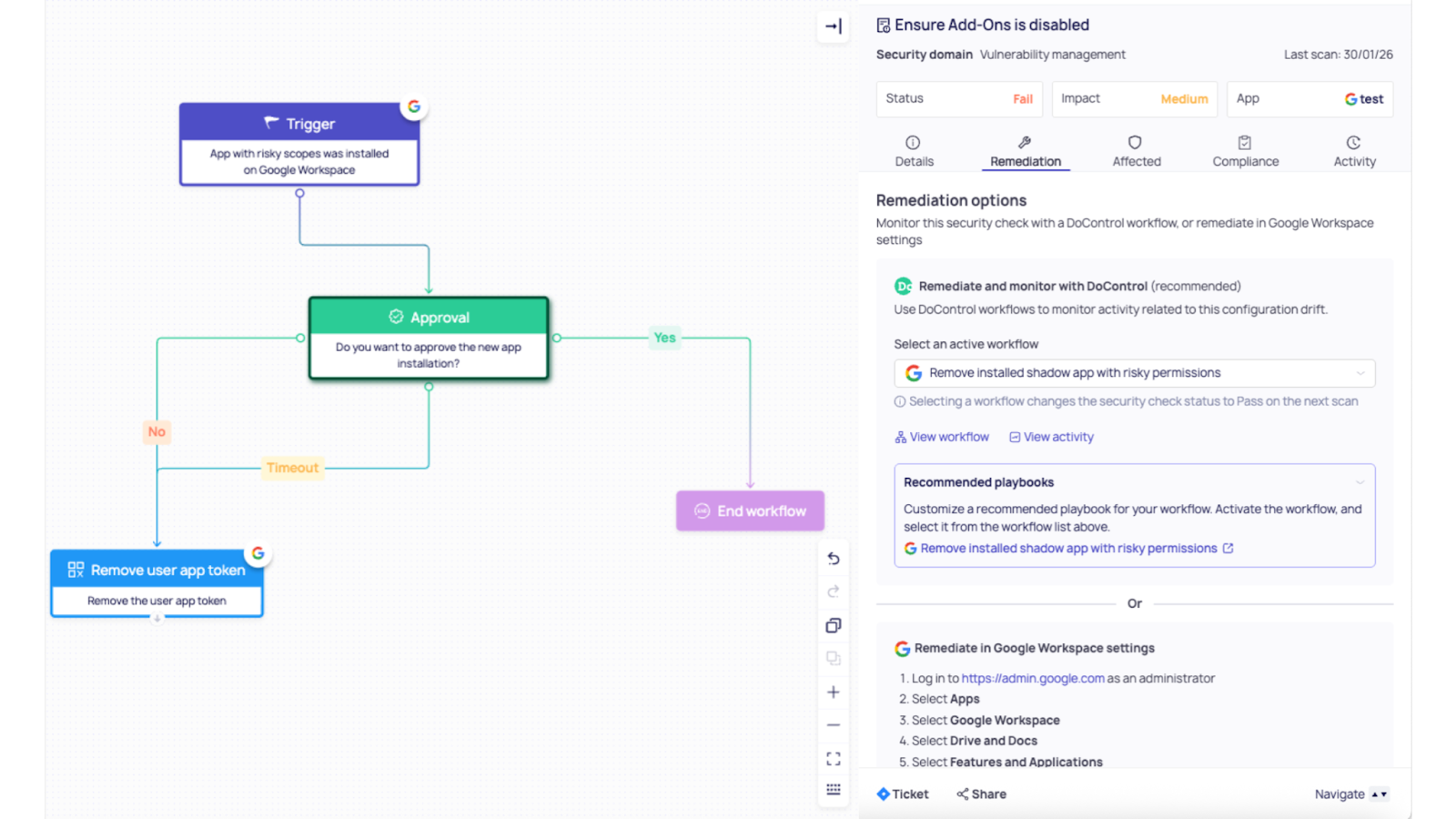
Example 2: OAuth Permission Creep (Shadow Apps)
A third-party app is connected with excessive permissions.
Workflow:
- Detect OAuth authorization event
- Evaluate app risk level and permission scope
- If unapproved → escalate or block
- Automatically revoke access if needed
Outcome:
- Prevents unauthorized data access
- Eliminates “shadow app” blind spots
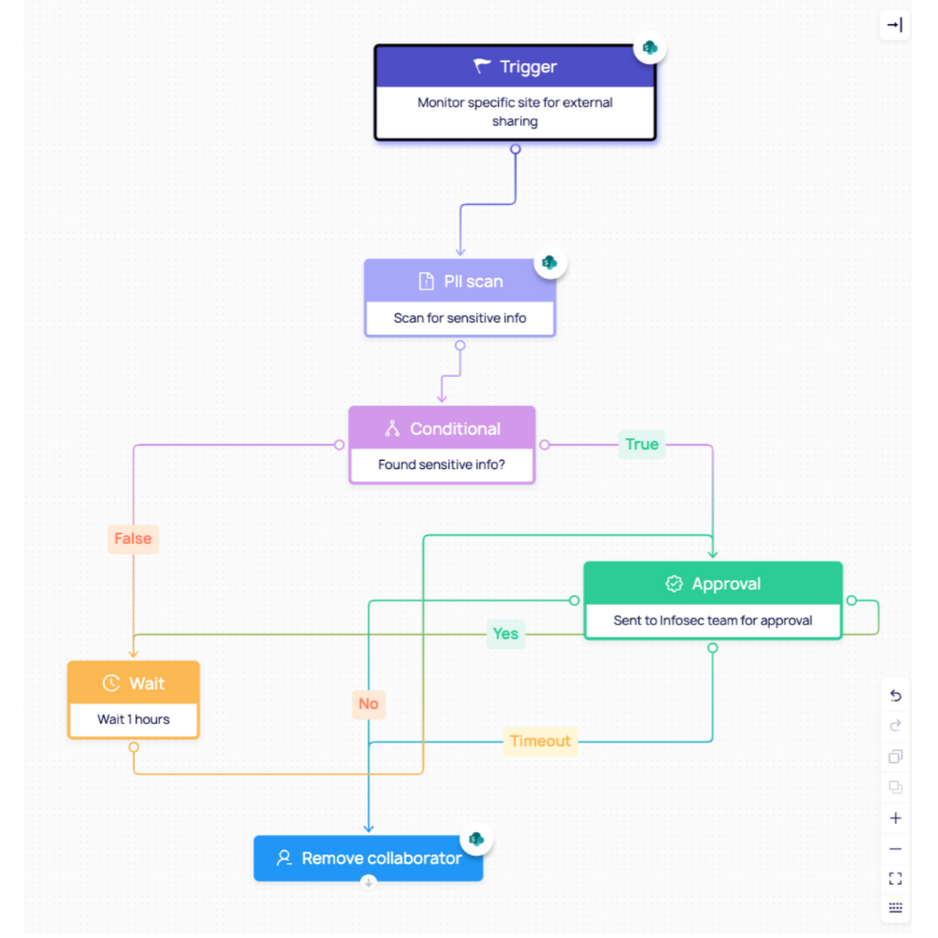
Example 3: SharePoint External Sharing Drift
An admin changes sharing settings to allow “Anyone” access.
Workflow:
- Detect tenant-level configuration drift
- Evaluate against baseline policy
- Automatically revert to approved configuration
- Apply additional guardrails (expiration, restricted sharing)
Outcome:
- Configuration returns to compliance automatically
- Risk is eliminated before exposure spreads
{{cta-1}}
6. Verification and Audit-Ready Evidence
Fixing a misconfiguration is only part of the solution.
You also need to prove it was fixed.
DoControl closes the loop by:
- Verifying that configurations have returned to a compliant state
- Recording what happened, when, and why
- Providing audit-ready evidence for compliance teams
This transforms security from:
- Periodic checks → to → continuous assurance
From Security Intent to Security System
This is the real shift.
Misconfiguration management is no longer about:
- Finding issues
- Creating tickets
- Hoping they get resolved
It’s about building a system where:
- Drift is automatically detected
- Risk is evaluated in context
- Remediation happens instantly
- Compliance is continuously maintained
DoControl turns your security policies into an always-on enforcement system - one that operates at the speed and scale of modern SaaS environments.
The Future of Misconfiguration Management
As SaaS environments continue to grow in complexity - and as AI applications, non-human identities, and integrations become more embedded into daily workflows - misconfigurations will only become more frequent and more difficult to detect.
The challenge is no longer identifying a single misconfiguration.
It’s managing continuous change across an ever-expanding attack surface.
A setting changed to unblock a workflow.
An integration added to meet a deadline.
An AI tool connected without fully understanding its data access.
Companies need to move beyond static policies and periodic audits, and instead adopt a model of continuous, context-aware enforcement.
Because in reality, there are countless ways misconfigurations can occur - but only one way to effectively manage them at scale: ensuring that every configuration change is evaluated in context, and every risk is automatically remediated in real time.
That’s the shift DoControl enables.
By combining visibility, context, and automated workflows, DoControl transforms misconfiguration management from a reactive process into an always-on system, one that continuously enforces security posture, eliminates drift, and protects sensitive data without slowing down the business.



