
The data loss prevention (DLP) market has never been more crowded, or more confusing. As organizations race to secure sensitive data across sprawling SaaS ecosystems, GenAI tools, and cloud infrastructure, the number of vendors claiming to solve the problem has multiplied just as fast as the threats themselves.
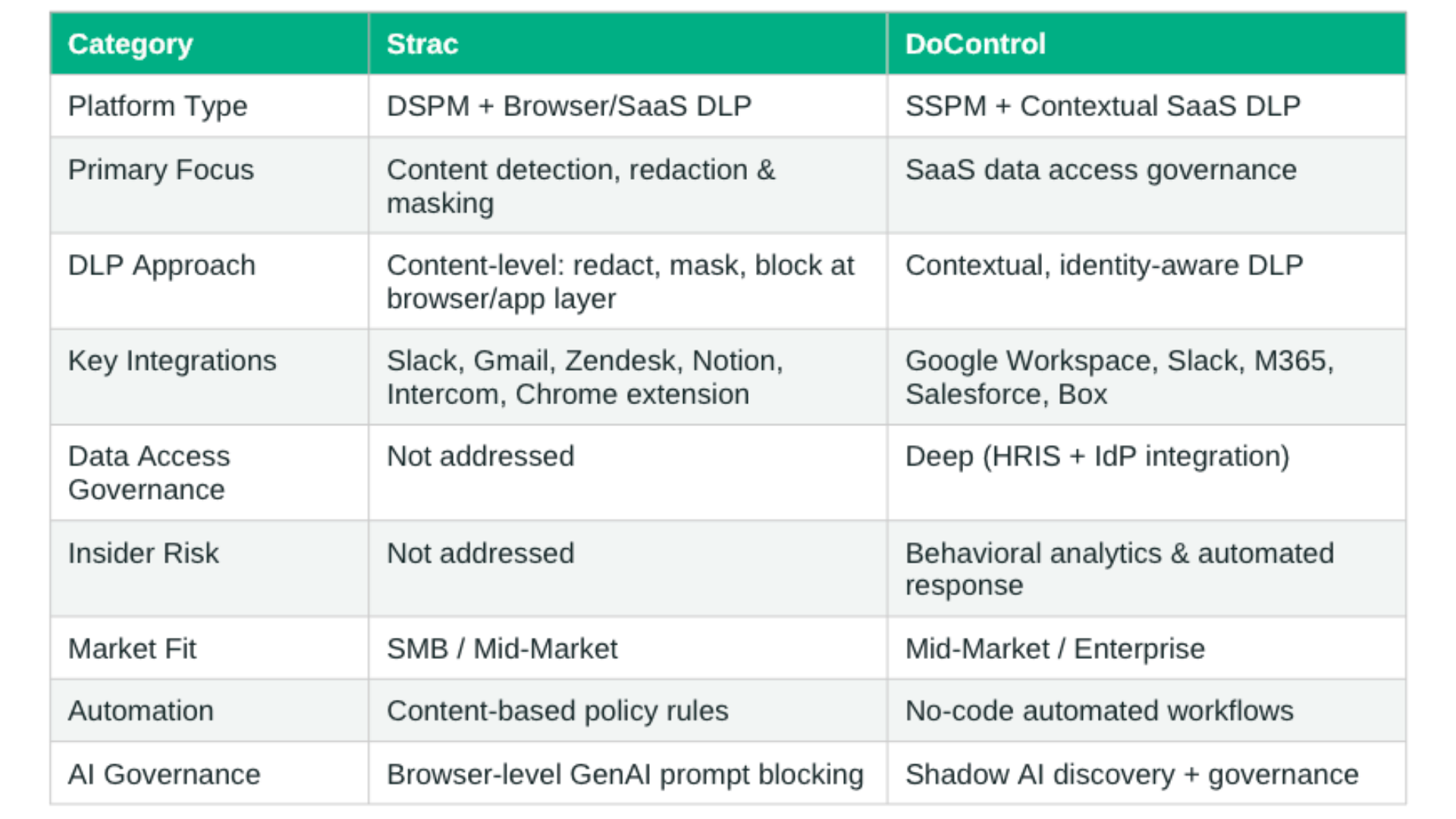
As it relates to DLP, two platforms frequently appearing in the same conversation are Strac and DoControl. On the surface, they may seem to occupy similar territory: both focus on protecting data in SaaS environments, both offer some form of DLP, and both are relatively modern entrants to the space.
But, a closer look reveals two fundamentally different approaches to the problem - different philosophies, different architectures, and ultimately, solving an entirely different SaaS data security problem.
This piece breaks down what each platform actually does, where they each shine, and why those distinctions matter as your organization evaluates what a modern DLP solution should look like.
Strac: DSPM + Browser DLP for Content-Level Data Protection
Lets dive into Strac, what they do, where they focus, and how they show up in the market today.
What Strac Is
Strac is a Data Security Posture Management (DSPM) and Data Loss Prevention (DLP) platform whose core capability is identifying sensitive data and acting on it at the content level - primarily through browser-based and SaaS application integrations. Put simply, Strac detects sensitive data and then redacts it, masks it, or blocks it from moving further. That is the scope of what it does.
This is an important distinction. Strac is not a data access governance platform. It does not manage who has access to what, does not remediate over-permissioned sharing, and does not evaluate whether a user should be interacting with a given file or dataset in the first place. Its lens is on the content of data, not the context surrounding it.
How Strac Works
Strac operates primarily through API-based integrations and a browser extension, scanning for sensitive data types (PII, PHI, PCI, credentials) across connected applications. When a match is found, the platform applies a content-level remediation action: redact the data, mask it, alert on it, or block it from being submitted or shared.
This makes Strac particularly useful for organizations that want to prevent sensitive data from appearing in places it shouldn't - like a customer SSN showing up in a Zendesk support ticket, credit card data in a Slack message, or confidential information being pasted into a ChatGPT prompt via the browser. Its Chrome extension is a key delivery mechanism for this kind of real-time, browser-level blocking.
Where Strac Focuses
Strac's deepest integrations are concentrated in communication and customer-facing tools:
- Slack - scanning messages and files for sensitive content
- Gmail and Outlook / Office 365 - email DLP with redaction
- Zendesk and Intercom - protecting support channels from PII exposure
- Notion - scanning collaborative workspaces
- Google Drive - some file-level content scanning
- Chrome browser extension - blocking sensitive data submission to GenAI tools and web apps
For its GenAI use case, Strac's browser extension can intercept what employees type or paste into tools like ChatGPT, detecting and blocking sensitive content before it reaches the model. This is a content-detection play - useful, but narrow in scope compared to a full shadow AI governance capability.
Who Strac Is Built For
Strac's content-first, browser-level approach has a ceiling when it comes to enterprise security requirements.
The platform does not address data access governance: it cannot tell you which users have access to which files, flag over-permissioned shared drives, or automatically revoke access when an employee is offboarded.
It also doesn't offer integration with HRIS or identity providers to add behavioral context to its detections. In practical terms, Strac can catch a credit card number in a Slack message, but it cannot detect that the person sending the credit card number is actually a departing employee sending it to a personal account.
This positions Strac well for SMB and mid-market organizations with lean security teams that need fast, low-friction protection against basic content leakage. However, as organizational complexity grows - more users, more applications, richer identity context - its capabilities begin to show their limits, and it’s not completely scalable.
It is a less natural fit for enterprise environments where data risk is inseparable from identity, access, and behavioral context.
TLDR; Strac is a DSPM + browser/SaaS DLP tool that detects sensitive data content, effective for content-level leakage prevention in communication tools. It does not address data access governance, identity context, or insider risk - making it better suited for SMB and mid-market than enterprise.
DoControl: SaaS-Native Security Built for Enterprise Complexity
Now, let's dive into DoControl: who we are, what we do, who our product is made for, and how our approach is different when it comes to posture management and SaaS DLP.
Who DoControl Is
DoControl is a SaaS Security Posture Management (SSPM) platform with a core focus on SaaS DLP and data access governance. Where Strac is primarily a data discovery tool with DLP capabilities bolted in, DoControl is architected from the ground up around the question: who has access to what data, why, and should they?
In today’s enterprises, data exposure doesn't happen just because sensitive content was left unprotected - it happens because the wrong person was granted access, a link to a sensitive file was set to public, a disgruntled employee was leaving the company and bring files with them, a third-party OAuth app was over-permissioned, or a misconfigured sharing setting made a file public.
There are a thousand ways that data can become exposed. DoControl is built to address that entire surface area - giving visibility, detection, and automated remediation to keep SaaS data protected at all times.
The Google Workspace and Slack Anchor
DoControl's deepest and most mature capabilities are rooted in Google Workspace security. It provides granular, automated governance across the entire Google ecosystem at a depth that Google's native tooling cannot match at enterprise scale. For security teams trying to get real visibility and control over how data moves within and out of Google Workspace, DoControl is the purpose-built answer.
Equally strong is DoControl's Slack coverage. As one of the primary collaboration surfaces where sensitive data is shared, discussed, and sometimes inadvertently exposed, Slack represents a high-risk channel for enterprise data.
DoControl monitors Slack for risky sharing behavior, sensitive data exposure in channels, and anomalous user activity - applying the same identity-aware, contextual lens it brings to Google Workspace. Together, Google Workspace and Slack represent the two highest-activity SaaS surfaces for most enterprises, and DoControl governs both with depth.
Beyond these core platforms, DoControl's coverage extends across Microsoft 365, Salesforce, Box, and other major SaaS applications - with a platform philosophy built around unified visibility across the entire SaaS stack, not siloed point integrations.
Contextual DLP: The Key Differentiator
DoControl's role in DLP is where it most meaningfully separates from Strac and much of the market. Rather than simply scanning for content that matches a sensitive data pattern, DoControl applies context to every detection.
The platform pulls from HRIS, IdP, and other signals to evaluate each event in context: who is sharing the file, what's the contents of that file, what is that person's role at the company, is this behavior in-line with their usual day-to-day actions or is it risky?
This contextual layer dramatically reduces false positives - a chronic pain point with traditional DLP - and enables the platform to catch genuinely high-risk activities that content-only scanners would miss entirely.
For example: a CFO sharing financial documents with an auditor during tax season looks very different from that same file being shared with a personal Gmail account by someone whose last day is Friday. DoControl knows the difference.
The platform monitors for data leakage, exfiltration, insider threats, account compromise, and anomalous access behavior - all within the context of the organization's identity fabric, baseline behavior, and every day baselines.
No-Code Automation at Scale
Another key part of DoControl’s DLP that takes protection a step further is the workflow engine. It’s a standout capability for enterprise security teams because it offers the scalable protection that growing orgs need.
Through no-code, automated remediation workflows, security teams can define precise policies that trigger automatic responses at scale: revoking access from hundreds of thousands of files in minutes, engaging end users directly via Slack or Teams bots to gather context on risky activity, or delegating self-remediation to the user themselves. The scenarios are endless, and security teams can make up their own workflows as their use cases expand.
This automation model is critical for enterprise environments where manual review is simply not operationally feasible. Security teams can't individually investigate every sharing event across a 10,000-person organization, which is why DoControl lets them define the logic once and trust the platform to execute.
Expanding AI Governance
Lastly, what sets DoControl apart in the DLP space is the active expansion of its AI security & governance capabilities, including shadow AI discovery, AI search governance (with tools like Gemini + Copilot), AI misconfigurations management, and intelligent, agentic alerting.
Additionally, the platform's AI assistant, Dot, allows security teams to query their environment in natural language, surfacing exposure risks across Google Workspace, Slack, Salesforce, and other connected platforms without requiring a query language or technical expertise.
TLDR: DoControl is a mature, enterprise-grade SSPM with contextual SaaS DLP and robust data access governance. Built for organizations that need identity-aware, automated, and scalable protection across complex SaaS environments - particularly those running on Google Workspace.
Buyers Guide: Key Things to Know
Strac focuses on discovering, classifying, and remediating sensitive data itself. Its core strengths include DSPM + DLP, OCR/ML-based classification, redaction and masking, and compliance-oriented protection for PII, PHI, PCI, source code, and IP.
DoControl focuses on securing how SaaS data is accessed, shared, and governed across collaboration tools. Its core strengths include contextual SaaS DLP, insider risk, identity and behavioral risk, shadow app/AI governance, misconfiguration detection, and automated remediation - all enriched with signals from IdP, HRIS, and EDR integrations.
Choose Strac if you care most about:
- Finding and redacting sensitive data across many channels like Slack, Gmail, Zendesk, Intercom, Notion, Google Drive, Salesforce, Jira, browsers, endpoints, and databases.
- Compliance-heavy workflows where redaction/masking is core, especially for customer support, email, and regulated data handling.
- Broad and general surface-area coverage spanning SaaS + cloud + GenAI + browser/endpoint controls.
Choose DoControl if you care most about:
- Oversharing, insider risk, and access governance in Google Workspace, M365, Slack, Salesforce, Box, Zoom, GitHub, Jira, and similar SaaS systems.
- Context-aware decisions rather than content-only DLP, using signals from identity, HR, and endpoint tools.
- Automated remediation workflows and governance of human + non-human identities, including shadow apps and AI-related exposure.
What the Market Needs Today
The SaaS DLP market is undergoing a fundamental shift. The old model - perimeter-based controls, content-matching rules, alert-heavy dashboards - was built for a world where data lived in predictable places. That world no longer exists.
Today's enterprise data lives in dozens of interconnected SaaS applications, flows continuously across internal and external boundaries, and is increasingly accessed by AI agents that don't behave like human users. The risks aren't just about what data looks like - they're about who is touching it, when, from where, and whether that behavior is normal.
What that reality demands is a security platform that is contextual by design, automated at scale, and deeply integrated with the identity and access layer of the organization.
It demands a platform that can secure not just the data itself, but the entire ecosystem around it: configurations, third-party apps, sharing permissions, behavioral patterns, and emerging AI usage.
Strac addresses a real and important part of this problem - particularly for organizations that need fast, broad data discovery across communication channels and cloud environments. For SMB and mid-market buyers, it's a strong and accessible option.
But for enterprises operating at scale, the demand is higher. The ability to apply identity context to every data access event, automate remediation without security team intervention, manage SaaS misconfigurations alongside data exposure, and govern the growing surface area of AI usage - these capabilities define what enterprise-grade SaaS security looks like in 2026 and beyond.



